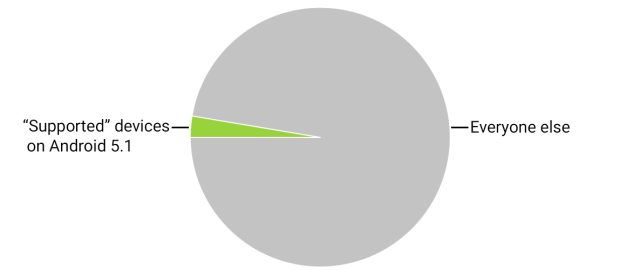
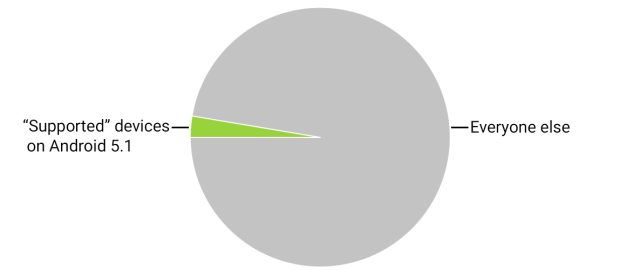
Supported Android 5.1 Devices that might be updated to patch security issues and All Others that will not be updated.
Posted on 08/11/2015 9:33:12 PM PDT by Swordmaker
Read the article at the link above. . . cannot be posted on FreeRepublic due to copyright issues.

If you want on or off the Mac Ping List, Freepmail me.
The hits for Android keep coming from the tech community. Here’s another one from Ars Technica relating to Androids broken update model in which NOBODY is really responsible to get critical security updates pushed out to users who are vulnerable to zero day exploits. . . especially for those users of older versions of Android.
Did they learn nothing from the failures of MicroSoft?
Well, now, let's not get completely freaked out by this.
Dayglored says, "Never underestimate the tolerance of the consuming public for crap."
Hell, most of the time the public SEEKS crap. Witness the current Administration. But I digress...
There will be more and more Zero Day exploits, and my prediction is people will just put up with them. Over and over.
They're mostly freakin' SHEEP. They are so used to crap they no longer care. They'll just put up with it. And the Android ecosystem will continue meandering along in its fragmented, diffuse fashion.
Is that a "solution"? Of sorts. Not a pretty one, certainly not a clean one, but I'll put money on it coming to pass.
That model just doesn't work under heavy pressure, and that's what the virus writers and other criminals are putting on Android -- pressure.
Google knows what they SHOULD do, but they can't, because every manufacturer customized Android, and no one patch works across the ecosystem.
My feeling is they asked for it, they worked for it, they got it, and they can have it.
Another day, another stunning security flaw in Android – this time hitting 55% of mobes
The Register — August 10, 2015Bug allows ordinary apps to gain control of gadgets
Video Fresh from sorting out the Stagefright flaw, Google has another serious security vulnerability in Android on its hands.
A privilege escalation hole allows normal apps to gain superpowers to snoop on a device's owner, smuggle in malware, and wreak other havoc.
The vulnerability, CVE-2015-3825, affects about 55 per cent of Android handsets – basically version 4.3 and above, as well as the current build of Android M.
Flaws in the OpenSSLX509Certificate class in Android can be exploited by an app to compromise the system_server process – and gain powerful system-level access on the device.
"In a nutshell, advanced attackers could exploit this arbitrary code execution vulnerability to give a malicious app with no privileges the ability to become a 'super app' and help the cybercriminals own the device," said Or Peles, security researcher at IBM's X-Force application security research team.
"In addition to this Android serialization vulnerability, the team also found several vulnerable third-party Android software development kits (SDKs), which can help attackers own apps."
It works like this. The attacker puts together an innocuous-looking app which, when installed, doesn't ask for permission to use data on the device, lulling the downloader into a false sense of security.
But once installed, the malware changes the memory values on the handset using the OpenSSLX509Certificate flaws, allowing it to escalate its privileges. The attacker can then introduce a replacement application for a legitimate app already on the device, and begin harvesting data once the device is rebooted.
The good news is that a patch for the flaw is available and there are no instances yet spotted of the vulnerability being exploited in the wild. The bad news is that most people won't have received the patch as yet, and many have to wait for one of the forthcoming monthly updates to get it.
The full explanation [PDF] of the flaw is being presented at the USENIX Workshop on Offensive Technologies (WOOT '15) in Washington DC. ®
"The good news is that a patch for the flaw is available and there are no instances yet spotted of the vulnerability being exploited in the wild. The bad news is that most people won't have received the patch as yet, and many have to wait for one of the forthcoming monthly updates to get it."
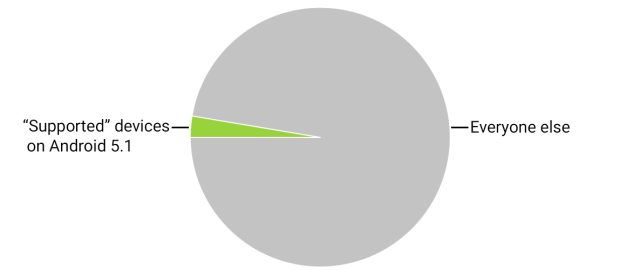
As Ars Technica pointed out something less than 3% of vulnerable Android users will ever receive the patch that will prevent them from being infected by this ZERO DAY malware's app because the patching system is ultimately broken.
Google is screwing up so bad they may leave an opportunity for Microsoft.
True, but never underestimate the ability of Microsoft to fumble an opportunity. :-)
And the really SAD news is that most Android users (like most users everywhere in the consumer marketplace) don't give a rat's ass about updates, vulnerabilities, patches... it all goes over their heads if they even bother to read about it.
Tonight I am not much enthused about the tech-buying public's awareness of how dangerous this stuff can be to their personal identity and liberty.
My 2-3 year old Android phone just received from Google,
Stagefright Detector.
Why and what’s in it for you to denigrate the world’s most used Mobile Operating System?
I'm also glad you like Android.
But I think you misunderstood my disgruntlement with a) most consumer users, and with b) the system by which Android updates can be pushed out to the user base.
I have nothing against Android itself as a product. Please note the difference between the product, and the things I expressed displeasure with, that happen to be related to the product.
If my Android tablet hadn’t already gone toes-up, I’d be upset about this. :’) One of the warehouse clubs has prev-gen iPad minis for something like $220, if I had the cash I’d probably replace the smoking pile of Android tablet with the mini.
A majority of American voters chose Barack Obama TWICE in the polls? Does the fact that he got the most votes make him the best? I don't think so, do you?
I'm not a Sales guy. I care about quality, not quantity. Now, it happens that Android is, overall, a very good platform. But a defense of it in terms of number of users doesn't impress me nearly so much as a defense from a technical point of view.
Just sayin'... :-)
So you’re an Apple guy and your stock has taken a hit.
But Apple Mac’s have their own security problems to contend with. Why not focus on those.
And i don’t write book size treatise posts knocking the competition.

What a load of non-sequiturs, topspirr. Dayglored as far as I know isn't worried about AAPL, nor did he write this article, nor is he primarily a Mac user. In fact, Dayglored runs the Windows ping list on FreeRepublic.
This article was written by one of the most well thought of and platform agnostic sites there is Ars Tecnica and their points are quite factual and well taken. Fewer than 3% of Android users will receive security updates for their devices. You are lucky you got one. . . But you are in the minority. Google is not in the direct chain to distribute to a high percentage of Android users because their device manufacturers control that, not Google.
Oops, I forgot to add you to the immediately previous reply. Sorry.
> So you’re an Apple guy and your stock has taken a hit. But Apple Mac’s have their own security problems to contend with. Why not focus on those.
No, I’m not an Apple guy, see my profile page if you actually are curious. I have no stock of any of these companies. I contend with all of the systems and their vulnerabilities, every day. I’m a system admin, among other things. You seem to be an Android guy. If so, enjoy it in good health.
Disclaimer: Opinions posted on Free Republic are those of the individual posters and do not necessarily represent the opinion of Free Republic or its management. All materials posted herein are protected by copyright law and the exemption for fair use of copyrighted works.