
Posted on 01/24/2019 8:28:38 PM PST by dayglored
Easily swapped hashed passwords gives Domain Admin rights via API call. Fix may land next month
Microsoft Exchange appears to be currently vulnerable to a privilege escalation attack that allows any user with a mailbox to become a Domain Admin.
On Thursday, Dirk-jan Mollema, a security researcher with Fox-IT in the Netherlands, published proof-of-concept code and an explanation of the attack, which involves the interplay of three separate issues.
According to Mollema, the primary problem is that Exchange has high privileges by default in the Active Directory domain.
"The Exchange Windows Permissions group has WriteDacl access on the Domain object in Active Directory, which enables any member of this group to modify the domain privileges, among which is the privilege to perform DCSync operations," he explains in his post.
This allows an attacker to synchronize the hashed passwords of the Active Directory users through a Domain Controller operation. Access to these hashed passwords allows the attacker to impersonate users and authenticate to any service using NTLM (a Microsoft authentication protocol) or Kerberos authentication within that domain.
Mollema wasn't immediately available to discuss his work due to time zone differences and the need to involve a media handler.
The attack relies on two Python-based tools: privexchange.py and ntlmrelayx.py. It has been tested on Exchange 2013 (CU21) on Windows Server 2012 R2, relayed to (fully patched) Windows Server 2016 DC and Exchange 2016 (CU11) on Windows Server 2016, and relayed to a Server 2019 DC, again fully patched.
Using NTLM, Mollema says it's possible to transfer automatic Windows authentication, which occurs upon connection to the attacker's machine, to other machines on the network.
How then to get Exchange to authenticate the attacker? Mollema points to a ZDI researcher who found a way to obtain Exchange authentication using an arbitrary URL over HTTP through the Exchange PushSubscription API using a reflection attack.
If this technique is instead used to perform a relay attack against LDAP, taking advantage of Exchange's high default privileges, it's possible to for the attacker to obtain DCSync rights.
Mollema describes several potential mitigations for the attack in his post. These include: reducing Exchange privileges on the Domain object; enabling LDAP signing and channel binding; blocking Exchange servers from connecting to arbitrary ports; enabling Extended Protection for Authentication on Exchange endpoints in IIS; removing the registry key that allows relaying; and enforcing SMB signing.
In a statement emailed to The Register, Microsoft avoided commenting on the specific vulnerability described by Mollema, but the wording of its coy, content-free reply suggests the company may issue a fix in February.
“Microsoft has a strong commitment to security and a demonstrated track record of investigating and proactively updating impacted devices as soon as possible," a Microsoft spokesperson said. "Our standard policy is to release security updates on Update Tuesday, the second Tuesday of each month." ®
Never a dull moment, when you've got an Exchange Server on site...

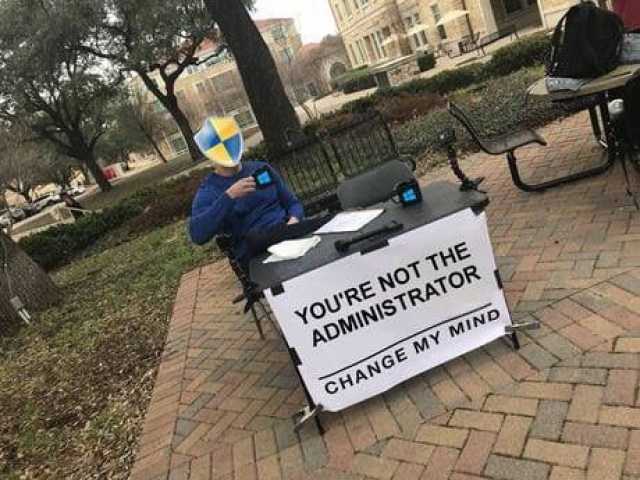
You're an admin! You're an admin! You're all admins, thanks to this Microsoft Exchange zero-day and exploit
I understand that now anyone can use the code to do whatever, but exactly WHAT is the "whatever"?
The article describes a vulnerability in the Exchange software that can lead to bad things in the server.
Yes, this doesn't apply to me at all.
Ah, GroupWare...
We want Enterprise admin privileges.
Wake me when there's real news.
I want that so I can set auto destruction for printers.
Yeah, but the vast majority of them have some convenient servers sitting right inside their corporate firewalls.
I'd disagree somewhat. According to the article it appears that you can remotely escalate your privs using the exchange server to do so. It is up to the domain admins to figure out some way to mitigate, but anyone in a position of authority in a corporate environment should take note of this, because it could make hacker's lives pretty easy until it is fixed. From what I understand, 70+ of all hacking is done by internal folks.
I have never run into a corporate printer that was secured to any degree at all. The big multifunction printers are actually big computers themselves. Many have webservers and such built into them that are never reset from the default admin passwords. They also tend to have FTP servers built in, and if they can receive faxes, they can also dial out.
Setting up these printers to do interesting things at odd hours is pretty easy.
I plainly and completely despise printers.
Good point.

"Damn, it feels good to be a gangsta!"
I am glad our company has moved our email to microsoft office 365..... our email is safe in the “cloud”.
Disclaimer: Opinions posted on Free Republic are those of the individual posters and do not necessarily represent the opinion of Free Republic or its management. All materials posted herein are protected by copyright law and the exemption for fair use of copyrighted works.