
Posted on 10/22/2016 1:02:41 PM PDT by Swordmaker
A distributed denial of service (DDoS) attack that on Friday severely impacted internet access for many U.S. web denizens was found to be in part enabled by a botnet targeting unprotected "Internet of Things" devices. For Apple, the revelation vindicates a controversial walled garden approach to IoT borne out through the HomeKit protocol.

DVRs and IP cameras like those made by Chinese company XiongMai Technologies contain a grievous security vulnerability and are in large part responsible for hosting the botnet.According to Krebs, DVRs and IP cameras made by Chinese company XiongMai Technologies, as well as other connected gadgets currently flooding the market, contain a grievous security vulnerability and are in large part responsible for hosting the botnet. As he explains, a portion of these devices can be reached via Telnet and SSH even after a user changes the default username and password.
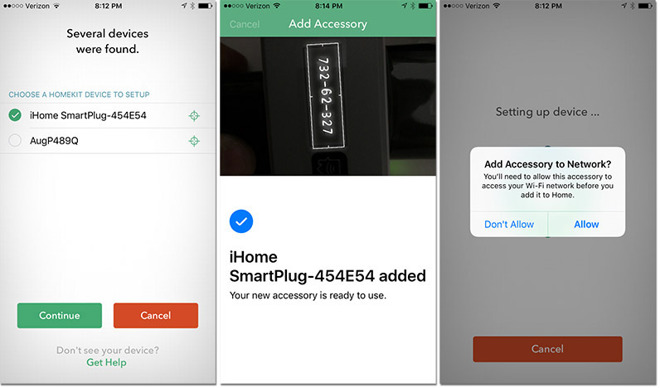
Apple uses the Secure Remote Password (3,072-bit) protocol to establish a connection between an iOS device and a HomeKit accessory via Wi-Fi or Bluetooth. Upon first use, keys are exchanged through a procedure that involves entering an 8-digit code provided by the manufacturer into a host iPhone or iPad. Finally, exchanged data is encrypted while the system verifies the accessory's MFi certification.
When an iPhone communicates with a HomeKit accessory, the two devices authenticate each other using the exchanged keys, Station-to-Station protocol and per-session encryption. Further, Apple painstakingly designed a remote control feature called iCloud Remote that allows users to access their accessories when not at home.
Accessories that support iCloud remote access are provisioned during the accessory's setup process. The provisioning process begins with the user signing in to iCloud. Next, the iOS device asks the accessory to sign a challenge using the Apple Authentication Coprocessor that is built into all Built for HomeKit accessories. The accessory also generates prime256v1 elliptic curve keys, and the public key is sent to the iOS device along with the signed challenge and the X.509 certificate of the authentication coprocessor.

The latest Apple/Mac/iOS Pings can be found by searching Keyword "ApplePingList" on FreeRepublic's Search.
If you want on or off the Mac Ping List, Freepmail me
Thanks for the head’s Up. . .
The is that the vast majority of people don’t won’t care enough to wall off their cheap IOT devices unless it affects them individually and directly.
Twitter being unavailable is an abstract problem, my baby monitor being off is a whole other matter.
Very interesting. However, the DDoS attack hit internet services - and could, I imagine, hit a service I use or, Heaven forefend, even FR.I saw a discussion elsewhere on FR of how to connect to FR when some useful but not essential servers are down. But it seemed to be targeted to Windows users. Any advice you would share about back up procedures for accessing FR under degraded Internet conditions?
As I recall there is a Yahoo discussion group for secondary communications when FR is down. I’ve recently let my yahoo emails go, so I don’t know for sure what the addressing is for that.
A 3,000 bit password ought to do it, that’s like a one in 1 followed by 1,000 zeros odds, making the 1 followed by 9 zeros for the Powerball seem like a sure thing.
But, if manufacturers can place open devices on the net at will, then this stuff will happen more and more.
God I hate regulation, but this is as much about safety as anything. Manufacturers must pass an internet device security safety certification, and those that don’t should be in jail.
In the meantime, IOT: you can GTH.
Find out what’s feeding off YOUR modem:
http://www.komando.com/downloads/2251/see-who-is-stealing-your-internet/2
“Each computer has a unique IP address, or Internet Protocol Address. Some computer hardware have addresses, too. They’re known as MACs, or Media Access Control.”
“As soon as you boot up Wireless Network Watcher, you’ll see all the detected devices come up on the list. You should be able to recognize all the devices on it. If you don’t, you know somebody is connected without your permission.”
Download instructions
Click on the blue link below. Scroll down the page until you see in purple, “Download Wireless Network Watcher with full install/uninstall support (wnetwatcher_setup.exe). Wireless Network Watcher will automatically download. Open the executable file and follow the step-by-step installation instructions.
http://www.nirsoft.net/utils/wireless_network_watcher.html
Tha is for the heads up!
Seems odd, the world we find ourselves in. The most despised computer company is the singular entity that does not track your personal information and will challenge the Govt over privacy rights.
Meanwhile, the “People’s Choice” makes no pretense that they are not spying on your personal email, texts or phone calls. They have been working with the NSA to bypass whatever security protocols are used by industry, and are working side by side with foreign entities who embed DOS attack malware within their products to attack American infrastructure from within.
Yet, these “patriots” cannot hate Apple more than they already do. It’s already at a psychosis level, and any factual information to show that Apple is actually doing “good” only serves to infuriate the psychopaths more.
No problem.
I’ve been somewhat dubious of IoT devices in my home. Not that I don’t like the convenience of automation. I’ve used X-10 for years but having “things” on the net, I’ve always been wary about.
The only “thing no” on the net in my house is the Nest thermostat. Bought before they sold out to google. And since it was also bought before the HomeKit framework, it doesn’t have the security built in.
I’ll go Honeywell in the future, I believe it is HomeKit compliant.
Phillips Hue is HomeKit, I’ll think about it to replace my X-10 dimmers when the price come down a bit.
You know, it’s funny; Back in the day I used to despise Apple. I was a PC guy. After my first computer (TRS-80 CoCo) I bought an IBM 5150. Had to take out a damn loan to buy it too. But after the MAC came out, no command line. It wasn’t a real computer.
Was a PC guy up until 2009, although I was getting tired of MS around 1998. Win 2000 was the last MS I used. (Had Vista that came on a ThinkPad for a couple of weeks before wiping it and installing Linux.
Then the iPhone came out. Finally, in 08/09 I bought my first MAC. It fit in my pocket! After many issues getting it to sync properly and consistently with iTunes running on W2K in a VirtualBox on my Linux ThinkPad, I bought an iMac.
Now here I am all these years later with an iMac, 2 Mac Minis, an original iPad, 3rd Gen iPad, IPad Air 2, two Apple TVs (3 & 4) and an iPhone 6.
I still have the iPhone 3GS that started me down this road. My GF lost the iPhone 5 I handed down to her when I upgraded to the 6.
She had to go out and get her own 6s. :-)
I’m happy with Apple. They work. And they do take pains to make them secure. And I think, in addition to all the engineering they put into the devices themselves, that their commitment to keeping things secure and private under the hood speak volumes.
Android is google. I don’t use google anymore. I’m not their damn product.
My first PC was the Commodore 64k back in 1978. Couldn’t afford a PC in college, so I took my programming and Engineering courses on a big IBM mainframe. Got my “own” PC when I worked for NASA. A 66 MHZ 486DX fully loaded. Back then I was investigating AI and neural network computing. Got some nice toys and advanced training.
From there I went to Austin and Motorola, who made the 68000 processors for Apple. There I designed testers for Motorola to test the 68xxx, RISC and advanced micro controller division. Got my first Mac issued to me there. Did my design (using MacPaint) drawing D sized drawings (yeah, 3 by 3 sheets of paper glued and taped together) with schematics covering the whole mess. No simulation. No emulation. Just draw the circuits on the Mac and hope they work as designed. Then debug the prototype. Did that for 9 years. Got to know the Mac very well. Even was one of the first to bring on the PowerPC Macs online.
Then off to the world of Intel R&D and PC design for 20 years. I bought my first Mac Mini in 2012 after seeing the mess Win8 was. I now manage engineers for the DoD and NASA. The DoD world still does the daily battle trying to make Win10 run the legacy software that they depend upon. Meanwhile, the SMART folks at NASA all use Apple MacBook Pros.
I get a kick of the idiots who “hate” Apple and have no clue as what one even is. They mock Apple users, yet my knowledge of Windows will dwarf what they know, and I use my Mac at home because it is so dependable. I can run, and do run WinXP, Win7 Pro and Win10 on my Mac with Parallels; while also running OSX.
The computer is a tool. It allows my brain accomplish more than it can without a computer. Whether that tool runs OSX, Windows, Linux, Chrome or even Ubuntu - I think I am better equipped to make that decision. Not some anti-Apple hater.
Swordmaker, any idea how an out of service iPhone linked as a security camera through an iOS approved app fairs in this regard? Should I dig out my AirPort Extreme to replace my U-verse router? Sounds like this is on a whole other level of authentication for that to make a difference.
As to the iPhone, security would depend on the model and how old it is. Anything capable of running iOS 8 and better on an iPhone 5s or above I think would be good. At my office we eschew using the Comcast provided WIFI router except for the free patient use, and use a locked down Apple AirPort Extreme for its security connected via Ethernet to the Comcast router and lock that connection down.
With those caveats, it could work fine.
What screwed up our office phones waltzed right through the Comcast firewall and into the Ethernet connected phone system. It probably would not have made it through our AirPort Extreme firewall and onto its Ethernet network. . . nothing downstream on that LAN was effected.
Interesting, thanks!
Disclaimer: Opinions posted on Free Republic are those of the individual posters and do not necessarily represent the opinion of Free Republic or its management. All materials posted herein are protected by copyright law and the exemption for fair use of copyrighted works.