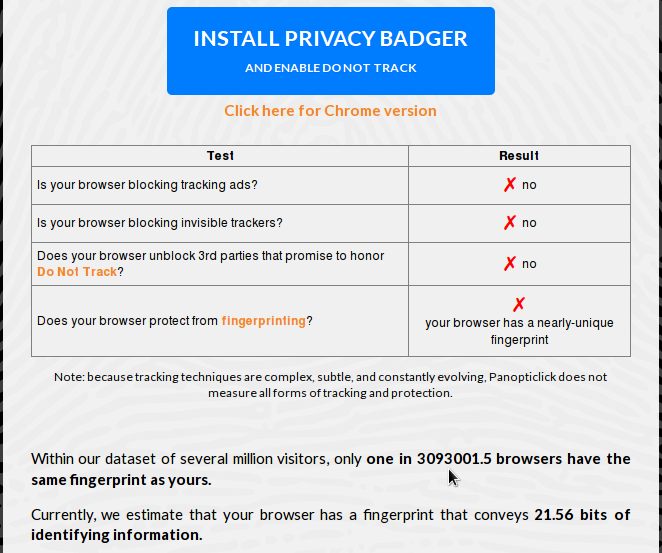
Figure 1: Browser fingerprinting under browser default settings
Posted on 12/30/2015 4:01:14 AM PST by ShadowAce
With recent revelations about browser fingerprinting, the race is on to find ways and means that will help reduce your browser's fingerprint, and with it, make it difficult for it (and you) to be tracked.
After trying Panopticlick yesterday, a tool released by the Electronic Frontier Foundation to help users determine if their browser is safe against tracking and fingerprinting, I set out to find out how to make my browsers less unique to trackers.
For the very paranoid, the results are not good.
Under default settings, a browser like Mozilla Firefox and Iceweasel emit very unique fingerprints, as shown in the result of a Panopticlick test in Figure 1. "Default settings" implies that DNT (Do Not Track) is disabled, and cookies are accepted. Pay special attention to how many other browsers have the same fingerprint as the target browser.
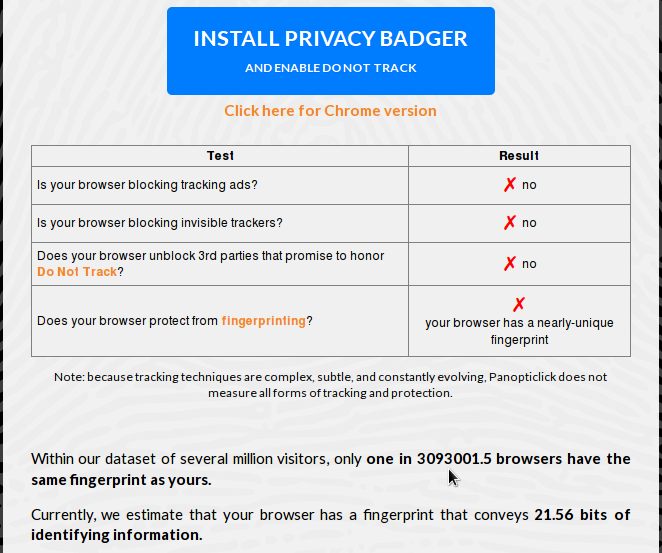
Figure 1: Browser fingerprinting under browser default settings
Enabling DNT makes no difference to the result of the test.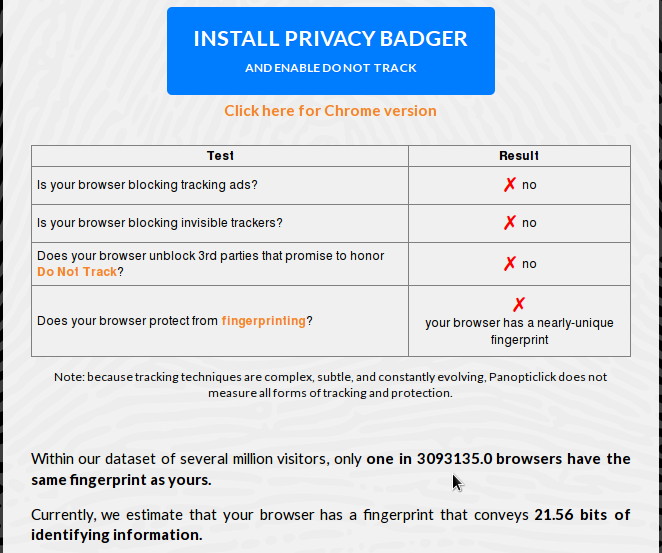
Figure 2: Browser fingerprinting with DNT (Do Not Track) enabled
Even with DNT and cookies rejected globally, the browser still has a unique fingerprint which was even worse than when cookies were accept.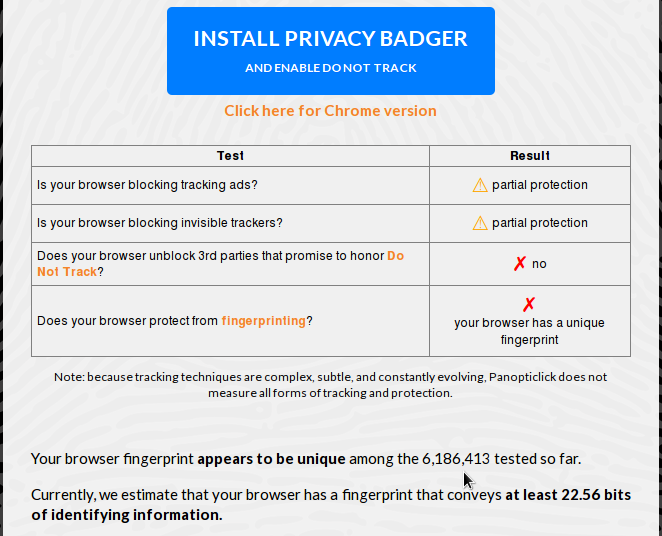 <
<
Figure 3: Browser fingerprinting with DNT (Do Not Track) enabled and cookies disabled
With Privacy Badger installed, still keeping DNT enabled and cookies rejected, the result is only as good as when DNT was enabled, which means not very good.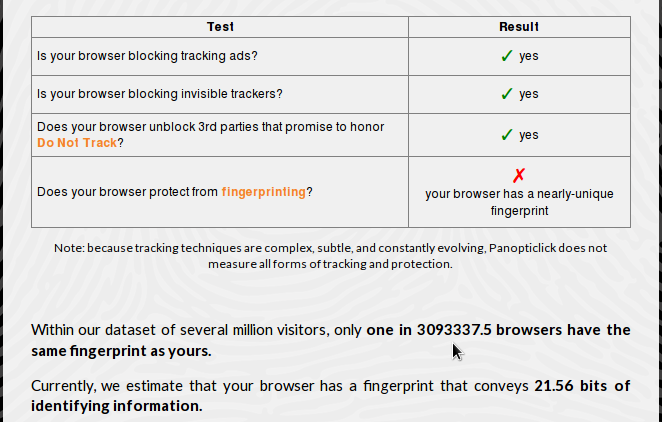
Figure 4: Browser fingerprinting with Privacy Badger installed
Throw NoScript in the mix, and your browser stands out like a sour thumb, which is counter to the expected result.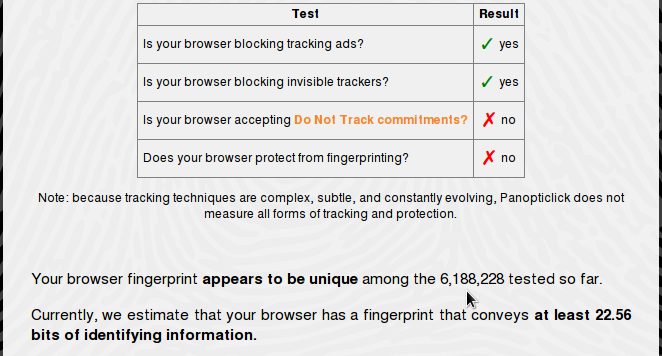
Figure 5: Browser fingerprinting with Privacy Badger and NoScript plugins installed
On a KDE desktop, there's an option in the System Settings that can be used to disable browser identification in Konqueror, the native KDE browser and file manager. It can also be used to give a fake identification to the browser.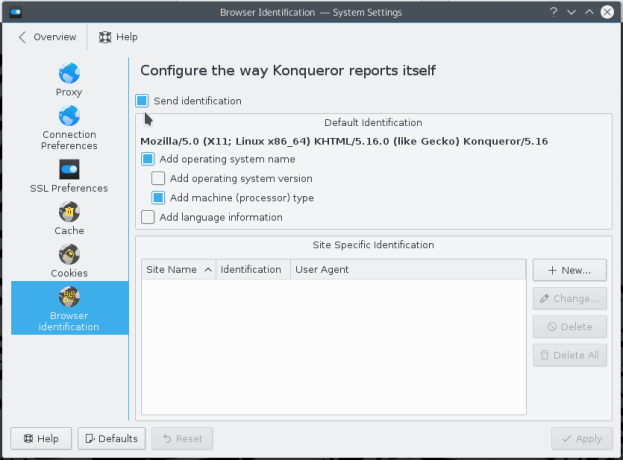
Figure 6: KDE Konqueror browser identification
However, disabling sending browser identification is useless, as it still leaves your browser with a unique fingerprint.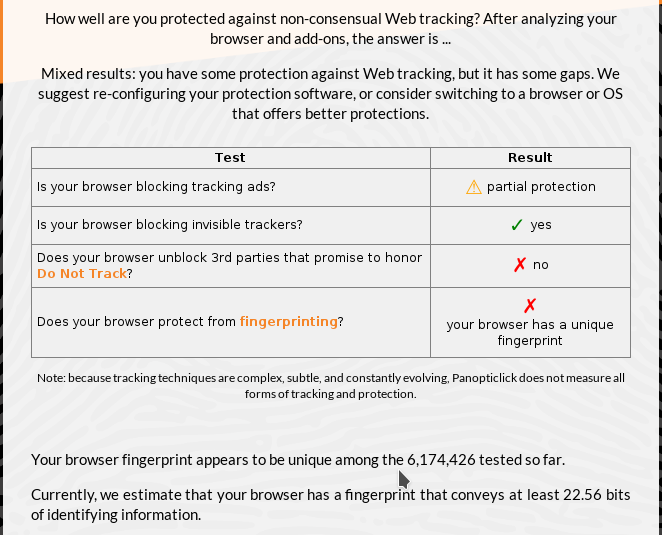
Figure 7: Browser fingerprinting test on Konqueror
So despite all the browser tools and options that can be deployed and tweaked to give a browser a less unique fingerprint, nothing seems to make any real difference. And from what I've seen so far, the more plugins installed and the more options enabled/disabled, the more unique your browser becomes. It's like getting your phone number on a "Do Not Call" list. To learn a bit more about this topic, the EFF has some suggestions here.

For later. Thanks.
The best way to prevent getting finger printed would be if your browser randomly browses thousands of different sites in the background, so it’ll clutter up the real data with garbage.
What other sites you may be browsing at the same time would not have an effect on what the browser is doing at that site.
Interesting, but let me try an analogy using a house:
-covering your windows
-blacking out your house number
-removing your mailbox
-gated entrance
-surveillance cameras
-camo netting over house to hide from google earth(and maybe street) images
Now, no one knows who’s in there are what they are doing and can’t get in to find out. But you stick out like a “sore thumb” as they say in the article and everyone thinks you are doing something.... aka “you must have something to hide”.
Seems the way to go is to build a honeytrap version of NoScript, Ghostery, ABP etc. which makes servers think you are actually running the garbage they are serving out.
Or, thinking bigger, basically a behind the scenes “virtual browser” running in default/generic mode that talks to the website while you view selected parts in your visible browser.
A better analogy (in terms of fingerprinting) is that you live in a tract house that is absolutely identical to every other house on the street—with the same house number, paint, and style.
yeah i guess the tract house is what i meant would be the default/generic browser, and with the modifications listed above for security/obscurity etc, you end up with something that sticks out like a sore thumb
Privacy died when anyone first plugged into a TCPIP network that routed to the rest of the world.
Essentially, AdNauseam quietly clicks every blocked ad, registering a visit on the ad networks databases. As the data gathered shows an omnivorous click-stream, user profiling, targeting and surveillance becomes futile.
Serious? It exists? I think I’ll get it.
Your ISP knows where you have been. The police regularly check with the ISP on the suspect to see what searches they made related to the crime like terrorism and PakistaniBrides.com
Your ISP knows that first hop. There are quite a few services that provide “anonymous” VPN services that also encrypt the data.
Yep. It’s all in the background so I can only assume it works.
bkmk
bump
Disclaimer: Opinions posted on Free Republic are those of the individual posters and do not necessarily represent the opinion of Free Republic or its management. All materials posted herein are protected by copyright law and the exemption for fair use of copyrighted works.