Posted on 09/21/2021 5:49:52 AM PDT by Red Badger
Mesa County, Colorado Clerk and Recorder Tina M. Peters has submitted a forensic examination report to the Mesa County commissioners. The report shows that a massive amount of election data was deleted and “destroyed” by the office of the Democrat Colorado Secretary of State Jena Griswold and Dominion Voting Systems, which performed a supposed system upgrade on the voting equipment in May. Luckily, Peters had the data backed up before it was destroyed, hopefully keeping alive the prospect of performing a full forensic audit of the 2020 election. (READ THE REPORT HERE)
https://bloximages.newyork1.vip.townnews.com/gjsentinel.com/content/tncms/assets/v3/editorial/0/47/047e4b26-187e-11ec-91f0-afc338816080/6145df5736676.pdf.pdf
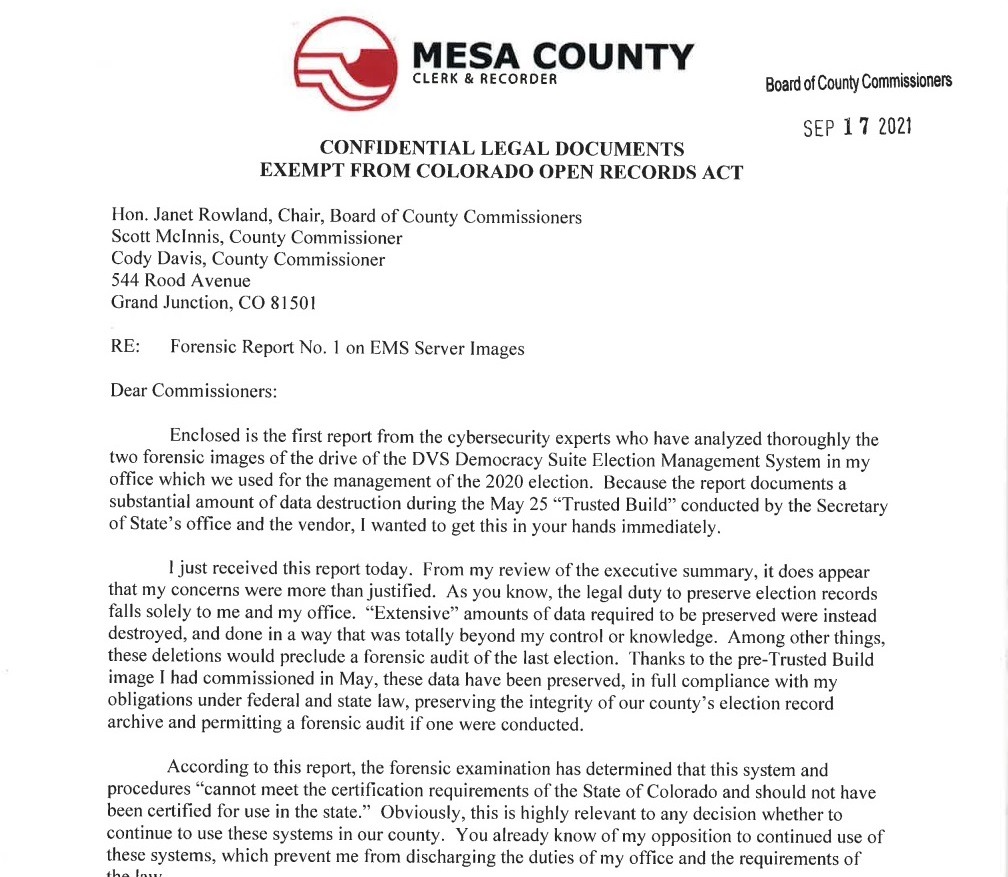
Mesa County Clerks and Recorder Tina M. Peters states in her letter to the county Commissioners: “Enclosed is the first report from the cybersecurity experts who have analyzed thoroughly the two forensic images of the drive of the DVS Democracy Suite Election Management System in my office which we used for the management of the 2020 election. Because the report documents a substantial amount of data destruction during the May 25 “Trusted Build” conducted by the Secretary of State’s office and the vendor, I wanted to get this in your hands immediately. I just received this report today. From my review of the executive summary, it does appear that my concerns were more than justified. As you know, the legal duty to preserve election records falls solely to me and my office. “Extensive” amounts of data required to be preserved were instead destroyed, and done in a way that was totally beyond my control or knowledge. Among other things, these deletions would preclude a forensic audit of the last election. Thanks to the pre-Trusted Build image I had commissioned in May, these data have been preserved, in full compliance with my obligations under federal and state law, preserving the integrity of our county’s election record archive and permitting a forensic audit if no one were conducted. According to this report, the forensic examination has determined that this system and procedures “cannot meet the certification requirements of the state of Colorado and should not have been certified for use in the state.” Obviously, this is highly relevant to any decision whether to continue to use these systems in our county.”
The report states (page 1): “Federal law requires the preservation of election records — which includes records in electronic or digital form — for twenty-two months after an election. Colorado law requires the preservation of election records for an additional three months beyond the Federal requirement…Forensic examination found that election records, including data described in the Federal Election Commission’s 2002 Voting System Standards (VSS) mandated by Colorado law as certification requirements for Colorado voting systems, have been destroyed on Mesa County’s voting system, by the system vendor and the Colorado Secretary of State’s office. Because similar system modifications were reportedly performed upon county election servers across the state, it is possible, if not likely, that such data destruction in violation of state and federal law has occurred in numerous other counties. The extent and manner of the destruction of the data comprising these election records is consequential, precluding the possibility of any comprehensive forensic audit of the conduct of any involved election.”
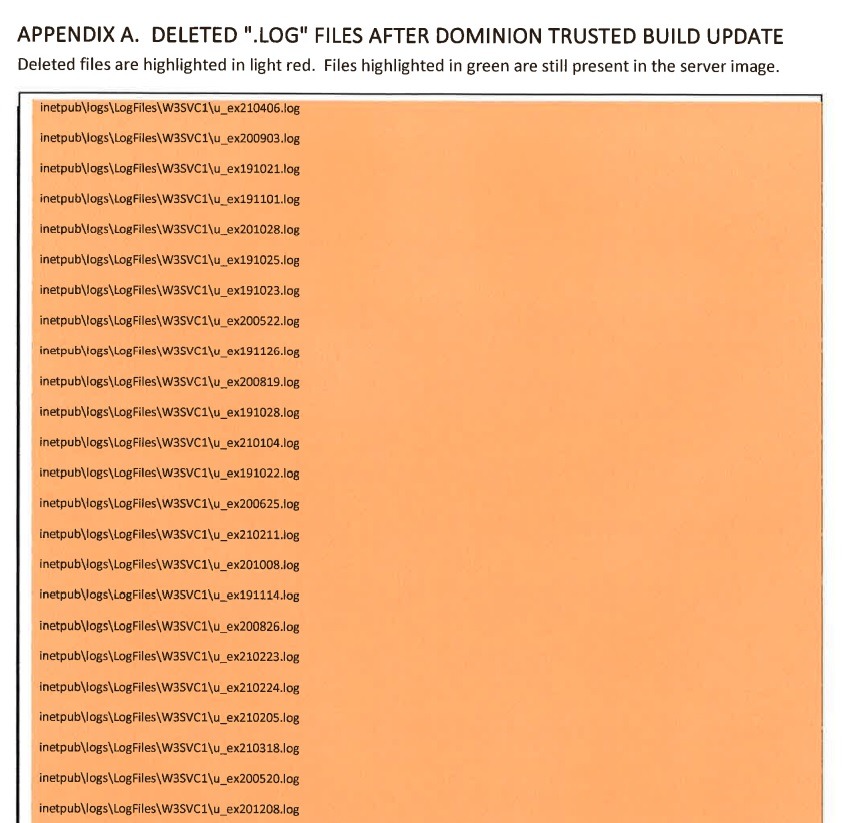
The report also documents the “DELETED “.LOG” FILES AFTER DOMINION TRUSTED BUILD UPDATE.”
Hotel California is not a solution.............................
You could not build a wall high enough to keep the Americans out of great America.
Sorry, I would not consider deleted inetpub\logfiles (IIS logs) “.log” Red-Handed.
I must wonder if Colorado Secretary of State will argue that the IIS logs are not considered election data.
The logs can be examined to determine what IP address access the server. Unless extra steps were taken, I do not expect the logs to record post and get information (vote data) contained in a SOAP/xml message.
Does Dominion software pass their data via query strings? Old school if so, that would be in the logs.
I wouldn’t recommend injecting any real-world analysis of that screenshot into this discussion. Any legitimate technical discussion is as dangerous as suggesting the earth may orbit the sun.
Tina got the receipts. Ha Ha Screw you Dominion.
Put on a dress and swish around for us.
I’m not the one spending my days on my knees slobbering in front of Trump.
Is it possible #15 works for Dominion?
Well there are plenty of people, you know, who were the leaders of, in the Congress, of challenging it," he continued, "that I just have not have on the show ever since then, and have purposely not had on the show, because frankly, I don't want to hear their crap."Fox News: "We report, you decide"
Tell a big enough lie long enough people will believe it...including the liars.
Chris Wallace(D) and the Fox News never-Trump cabal.
That’s what happens when people feel they have been cheated - due process goes out the window. The fraudsters are playing with fire. If they can’t bring about their totalitarian surveillance state in time, the blowback is going to resemble the ending scenes of Spartacus.
At a time when it mattered, I suggested a 10 mil reward, a pardon, and witness protection for someone who participated in this and came forward to turn in the organizers.
A new leftist propagandist joins FR. You guys control most of the rest of the media. We recognize your BS here.
So who has the authority to arrest those who destroyed evidence? (🥱😴)
Dominion needs to be sued, prosecuted and put completely out of business.
Don’t worry - you can cancel me. And with no irony, whine about Twitter bans in the next thread.
Disclaimer: Opinions posted on Free Republic are those of the individual posters and do not necessarily represent the opinion of Free Republic or its management. All materials posted herein are protected by copyright law and the exemption for fair use of copyrighted works.