
The heeled hacker's toolkit.
Posted on 08/24/2015 4:12:58 AM PDT by markomalley
Mildly nsfw A Chinese hardware hacker has built a penetration testing toolkit built into high-heeled shoes.
The WiFi-popping platforms were forged in a 3D printer and contain spacing so that hacking hardware can be hidden to bypass strict security checks in place at datacentres and the like and later retrieved.
The hacker and pen-tester, who goes by the handle "SexyCyborg", showcases the heels she dubs Wu Ying shoes, named after the famed "shadowless kick" that Chinese folk hero Wong Fei Hung used to distract opponents.
The hacker showcased the shoes in a post (somewhat NFSW) showing how a router, backup battery, and lock-picking set can be concealed from security guards while on red team penetration tests.
"With my shadowless shoes I distract the target with my upper body and they don’t see the real danger on my feet," she writes.
"Each shoe has a drawer that can be slid out without my having to take the shoes off [which] can be customised for various payloads.
SexyCyborg says "... my right shoe contains a pen testing drop box which is a wireless router running OpenWRT with a built in rechargeable battery that could either be left running inside the shoe (for war-walking, wifi sniffing and logging) or could be removed and plugged into a convenient open network jack [gaining] gain remote access anytime via SSH tunnel."
(image snipped)
Social engineering penetration testers have various tricks they use to gain access to restricted areas. Staff access badges are frequent targets for cloning as they dangle from waist belts, while polished silver-tongue swindling is a staple for conning helpful employees into opening doors.
She says bringing hacking tools into a security facility by way of a handbag is too conspicuous while policy typically demands mobile phones are left outside.
 The heeled hacker's toolkit. |
Her skimpy outfit is also a tactical decision; "My typical clothing does not leave room to hide anything, but that’s all the more reason they would not be suspicious of me," she says.
The Chinese hacker installed the OpenWRT firmware on a TL-MR10U router concealed in a cavity within the heel that runs Wispi and Jasager. Those tools can help the heeled hacker set up rogue access points that trick employees into punching in their enterprise credentials into fake phishing login pages.
"Wispi and pen-test drop boxes should of course should only be experimented with at home for educational purposes; while it’s good to know about this stuff, always obey your local laws," she says.
Hackers can "go all out" and run Kali and or PwnPi on a Raspberry Pi but the pen tester warns the shoes may start to get heavy.
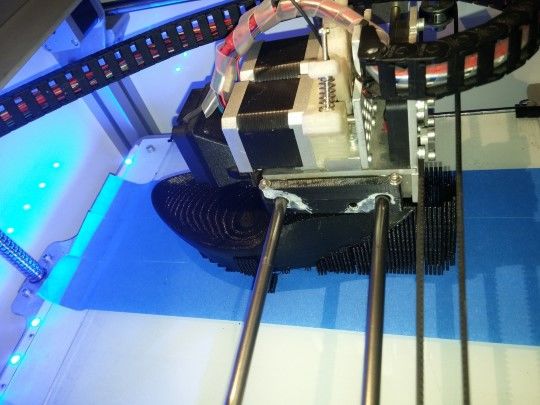 The 3D printer in action. |
The hacker has released the 3D-printer blueprints for enterprising hackers to follow and says the heels are strong and safe to wear.
Maybe there’s a market for one-person EMP chambers to kill any hidden electronics.
Is that her? She looks fake, including her face.
She is a very bad girl and must have a firm spanking.
If you have ping list put me on it... studying for my CEH right now
That’s what I’m betting on.
That’s the photo with the article. She appears, um, unbalanced.
Disclaimer: Opinions posted on Free Republic are those of the individual posters and do not necessarily represent the opinion of Free Republic or its management. All materials posted herein are protected by copyright law and the exemption for fair use of copyrighted works.