Posted on 07/05/2011 6:20:29 AM PDT by ShadowAce
A plan to populate the internet with hundreds or thousands of new top-level domains has security researchers pondering some of the unintended consequences that could be exploited by online criminals. Some of the scenarios aren't pretty.
Consider the mayhem that might result from addresses that end in “exchange,” “mailserver,” “domain,” or other strings that are frequently used to designate highly sensitive resources on corporate and government networks.
If a glitch ever caused an email program or other application to reach one of these external addresses, instead of the internal server carrying the identical host name, the outcome could prove disastrous for the stability of the internet.
“There's going to be a lot of cause for confusion, and it's going to make things a lot more ambiguous than they are today,” said H D Moore, CSO of Rapid7 and chief architect of the Metasploit penetration testing project. “TLDs could break widely used software products.”
An even more dire scenario would arise if online criminals intentionally acquired a strategically named TLD and used the incoming connections to harvest passwords or mount attacks on the connecting clients.
A corporate laptop, for example, that connected to an airport hotspot rather than the normal enterprise network might connect to the domain name “mailserver” controlled by hackers, rather than the trusted internal server by the same name. Similar attacks could be waged with other strings, including “wpad,” “lan,” and “local.”
The handwringing comes two weeks after the Internet Corporation for Assigned Names and Numbers approved a measure allowing anyone to submit applications for virtually any TLD. The change could add hundreds or thousands of new suffixes over the next few years that contain brand names such as “Nike” or “Ford,” as well as generic words such as “bank.”
Right now, there are fewer than 300 TLDs, and most of them contain nondescript two- and three-letter suffixes such as .com or .uk.
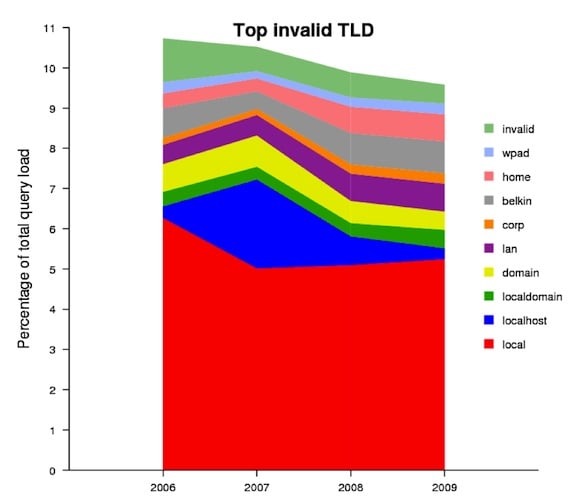
Despite criticisms from some that the security concerns are overblown (more about that later), there's ample reason to take them seriously. According to data (PDF) presented in 2009 by the DNS Operations, Analysis, and Research Center, 10 invalid TLDs represented 10 per cent of the total query load on the internet's DNS. Those non-conforming TLDs included “wpad,” “domain,” “localdomain,” and “localhost,” strongly suggesting that huge numbers of applications have for years unwittingly leaked local host names onto the internet.
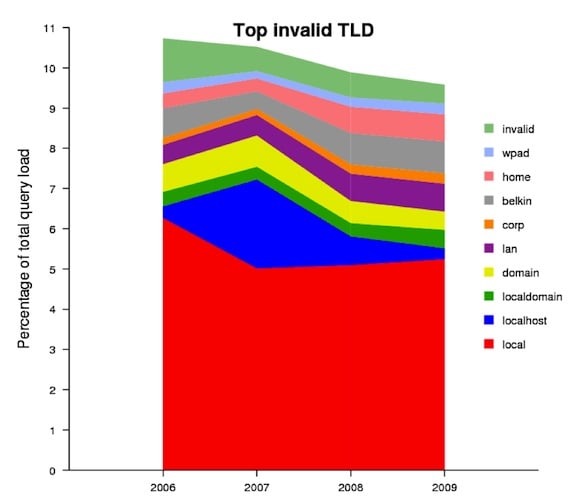
Traffic for top 10 invalid TLDs. Source: DNS Operations, Analysis, and Research Center, 2009
As DNS expert Paul Vixie recently explained, software applications that interact with host names on internal networks should never query the internet's domain name system for their location. But in practices, things don't always work that way. There's no guarantee that a so-called single-label internet address will be reachable on the internet, but likewise, there's no guarantee it won't.
“They won't work reliably,” Vixie told The Register. “The point you're getting at is they will also not fail reliably, so if somebody types a name without a dot, it might actually work.”
Indeed, depending on the browser and operating system used, a handful of sites are already accessible by typing nothing more than the TLD into the address bar. Using Mozilla Firefox on Mac or Ubuntu computers, it's possible to reach ac merely by pointing the browser to “ac” (minus the quotes). The same is true for io and tm. Google Chrome on OS X and Ubuntu will also access these sites with a little coaxing.
Using a Windows XP SP3 computer, The Register was unable to reach any of the three sites above. But according to researcher and software developer Marsh Ray, a home PC of his that ran Windows Vista connected just fine, and to make matters more dire, the lack of a dot in the address fooled the operating system into placing the site in the “Local Intranet Zone,” which Windows reserves for trusted internal addresses that don't require the same security defenses as external ones.
The potential for abuse, he said, is definitely there.
“It doesn't help you if you run Windows and it accepts *any* name without dots in it as the more-trusted 'local intranet zone,'” Ray, who works for two-factor authentication service PhoneFactor, wrote in an email. “There's simply *no* fixing this problem at ICANN. I know guys inside Microsoft who are feeling a little annoyed about the idea of .apple serving web pages into their intranet zone.”
Not everyone agrees the TLD expansion carries such risks. Among the skeptics is Dan Kaminsky, a DNS expert and the chief scientist for security firm DKH.
“It's a bunch of FUD,” he said, referring to the scenarios painted by Ray and other critics. “Yes, if domains like wpad or localhost or localdomain were assigned, bad things might happen. Those domains aren't going to get assigned. It's not like there aren't layers of approval that have to go in place to get a top level domain.”
The ICANN approval process Kaminsky was referring to calls for a $185,000 fee to be tacked onto each TLD application. The hefty charge is intended to winnow down the number of requests, so each one can be closely examined by human beings to make sure the proposed names comply with trademark and security criteria.
“This is not like going to GoDaddy and spending $40 for a domain,” Kaminsky added. “You have a $185,000 fee, and ICANN has a board that looks at this stuff.”
ICANN rules at the moment don't prohibit the registration of any specific TLDs, but the organization's Security, Stability and Advisory Committee in November issued a report (PDF) that obliquely hinted at the security threats end users might face if DNS servers stopped responding to certain invalid TLD requests with the standard "NXDOMAIN" error messages.
“Whereas the NXDOMAIN forces the querying application or user into an error resolution condition, the referral response from a root name server could cause recursion to continue (consider again the .lan scenario describe[d] above), with unpredictable results for the user,” the authors wrote.
The brief reference, buried near the end of the 10-page paper, doesn't warn of the huge opportunity a properly chosen TLD represents to a skilled attacker. What's more, it fails to acknowledge the large number of names that could wreak havoc.
TLDs such as “calicense” (PDF here), for example, or “isatap” could be exploited by attackers to breach corporate or government networks, since those strings are widely used to denote local resources by those deploying software from Computer Associates and Microsoft respectively.
“Basically, if you can control the ISATAP root TLD, you can talk to everyone's Windows machine on the planet with [IPv6 setting] 6in4 configured, since the ISATAP 'router' will be used,” Moore, of Rapid7, wrote in an email. If such names resolve at the DNS root level it “will destroy security on the internet as we know it.”
Even TLDs containing innocuous-sounding words such as “accounting,” “mail,” and “search” could potentially be exploited, given the huge number of networks that use them to route local traffic.
“They're going to ignore all the small guys,” Ray, the PhoneFactor researcher, said, referring to the ICANN people responsible for vetting TLD applications for security problems. “Every little admin who hardcoded a short host name in some script somewhere is going to risk collision with a global top level domain unless that capability is somehow disabled entirely, which would imply that you can't actually serve anything from these global top level domains.”
F-Secure Chief Research Officer Mikko Hypponen recently speculated on the damage that could be done with a TLD consisting of the number 1, since it would allow the owner to create a routable host called 127.0.0.1, the IP address for “localhost.”
“While I'm at it, I'll also register 'intra', 'smtp', 'local' and 'mail'...maybe also 'con,'” he said in a follow-up tweet.
The longer term solution to problems such as these, Kaminsky and Vixie said, is to revamp DNS servers so that so-called A records never map an IP address to a single-label address.
Their proposal would close the security hole, but as Ray suggests, it would come at considerable cost. One of the presumed reasons a group or corporation would be willing to spend $185,000 for a TLD such as “nike” or “bank” is to have a website or email address that uses that string alone as the domain name (think http://nike/ or marketing@nike, as opposed to http://www.nike.com or marketing@nike.com). If dotless addresses are eliminated from A records, that won't be possible.
There's no indication ICANN or the Internet Engineering Task Force will be able to enact such a sweeping change by January, when ICANN will start accepting applications for the new TLDs.
The means that members vetting the proposed names better act as if the Sword of Damocles is dangling over their heads. The network they destroy could very well be their own. ®

Shouldn’t you be appending your domain name for your internal subdomains?
For example, your internal mailserver that is only reachable on the subnet should be mailserver.bigcompany.com. If someone tries to use it without VPN’ing into the subnet, it is just not found.
I thought the internet was out of IPs. Is this the new disaster?
Guess it’s time to call in AL Gore to fix this problem.
A lot of companies use the same domain internally and externally. While this makes functionality great for employees that can work from where ever with the same configuration, it is a security challenge. 2 factor authentication is a nessecity.
That is a different issue.
IP addresses are translated into user-readable addresses, like www.freerepublic.com.
So now, instead of ".com", we will be getting a lot of others.
Yes I know. Its a bunch of chicken little hyperbole.
Of course changing things could break the ‘internet’. There are already a gazillion ways to break the ‘internet’.
The govts move to add their control is a much bigger concern.
This is a completely bogus argument. TLDs are a license to print money. If a company like McDonalds wants to protect its trademark, they have to buy up the domains in each TLD. Multiply that times an insane number of new TLDs and you have the makings for a great expense for companies, and great profit for the "owners" of the TLD.
What is the point of this garbage anyway? I don't recall a groundswell of demands from anyone but domain registrars (who are the ones who stand to profit handsomely from this), for new TLDs. I really don't see the need for internet namespace to be more complex and confusing than it is now, unless you want to make scammers's lives easier.
One thing that I'm going to start taking a look at is a way to filter my DNS queries so that my resolver will only allow specified TLDs. Personally, I have no desire to go to any domain other than those which we used to call the 'free world'. I realize that won't solve all associated potential problems, but it would be a start. It should be fairly easy to do through dnsmasq or something similar. You should be able to 'whitelist' domains/TLDs that you want to be able to use and 'blacklist' those that are problematic.
From /etc/dnsmasq.conf:
# Never forward plain names (without a dot or domain part)
# domain-needed
I've been using this program for some time to speed DNS queries on my local workstation. After poking through the config file, I see that it has a lot more power than I thought. I bet it would be possible to make it block TLDs like I was metioning above. Will have to look into it for sure.
You are 100% correct, this whole “problem” is bureacracy in action
And probably government intervention
They want to tax the heck out of that $185K
Disclaimer: Opinions posted on Free Republic are those of the individual posters and do not necessarily represent the opinion of Free Republic or its management. All materials posted herein are protected by copyright law and the exemption for fair use of copyrighted works.