- - -
Tried to find some worthy info in the files from Bob Zeidman. Using his text file, "Exhibit D - Target_MachineID_HEX.rtf", here are the first six lines:
{\rtf1\ansi\ansicpg1252\cocoartf2513
\cocoatextscaling0\cocoaplatform0{\fonttbl\f0\fswiss\fcharset0 Helvetica;}
{\colortbl;\red255\green255\blue255;}
{\*\expandedcolortbl;;}
\margl1440\margr1440\vieww10800\viewh8400\viewkind0
\pard\tx720\tx1440\tx2160\tx2880\tx3600\tx4320\tx5040\tx5760\tx6480\tx7200\tx7920\tx8640\pardirnatural\partightenfactor0
Those first six lines are RTF file info, plus sometimes, info about the computing device (and/or its OS), and about software involved. Such lines vary, depending sometimes upon the computer in, and depending upon the software used to create the RTF file.
That is a bit of a hint, that you might be able - over time - to stumble upon the software that created the RTF file, by discovering a match or "close enough" in the pattern of those six lines, with the resulting RTF file created by some software that you use.
Reference materials for understanding RTF:
Rich Text Format (RTF) Version 1.5 Specification
https://www.biblioscape.com/rtf15_spec.htm
RTF Pocket Guide:
https://www.oreilly.com/library/view/rtf-pocket-guide/9781449302047/ch01.html
- - -
The first data line:
\f0\fs24 \cf0 \'cc\'df\'b3\'b7Q.WVn\'a8_\'d4.q\'c2.`\'d5Y\'c5\'be\'c1.i#\'fe.P\'dar?.(\'a0\
. . . has ASCII characters that represent (can be converted to) HEX values. For example, the character string \'cc (backslash apostrophe c c) - ignore the backslash apostrophe characters, and convert the ASCII characters "cc" (no quotes) to HEX.
The following lines illustrate the conversion.
NEW LINE FOLLOWS
REFERENCE: https://www.oreilly.com/library/view/rtf-pocket-guide/9781449302047/ch01.html
| \f0 | font associated with the number 0 in the font table | |
| \fs24 | font size 24 | |
| cf0 | foreground color associated with the number 0 in the color table |
REFERENCE: https://www.rapidtables.com/convert/number/ascii-to-hex.html
| \'cc | ASCII text converted to HEX | 63 63 | ||
| \'df | ASCII text converted to HEX | 64 66 | ||
| \'b3 | ASCII text converted to HEX | 62 33 | ||
| \'b7Q.WVn | ASCII text converted to HEX | 62 37 51 2E 57 56 6E | ||
| \'a8 | ASCII text converted to HEX | 61 38 5F | ||
| \'d4.q | ASCII text converted to HEX | 64 34 2E 71 | ||
| \'c2.` | ASCII text converted to HEX | 63 32 2E 60 | ||
| \'d5Y | ASCII text converted to HEX | 64 35 59 | ||
| \'c5 | ASCII text converted to HEX | 63 35 | ||
| \'be | ASCII text converted to HEX | 62 65 | ||
| \'c1.i# | ASCII text converted to HEX | 63 31 2E 69 23 | ||
| \'fe.P | ASCII text converted to HEX | 66 65 2E 50 | ||
| \'dar?.( | ASCII text converted to HEX | 64 61 72 3F 2E 28 | ||
| \'a0 | ASCII text converted to HEX | 61 30 | ||
| \ | (probably end of line) |
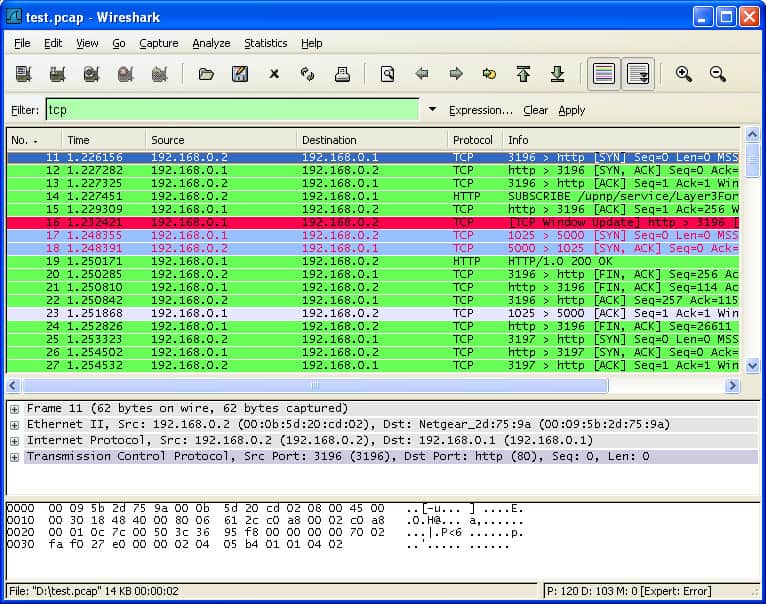
THAT "NEW LINE" ARRANGED IN THE FORM AS SEEN IN THE Wireshark IMAGE:
63 63 64 66 62 33 62 37 51 2E 57 56 6E 61 38 5F
64 34 2E 71 63 32 2E 60 64 35 59 63 35 62 65 63
31 2E 69 23 66 65 2E 50 64 61 72 3F 2E 28 61 30
But, you still need the actual year 2020 election data traffic packets, in order to find a match - and Mike Lindell did not provide the traffic packets data in any meaningful, readable form.
If "Exhibit D - Target_MachineID_HEX.rtf" is actually a conversion from a PCAP file, and therefore it can be flipped back to being that PCAP file, the software program for doing that work, is a major missing link. IMHO
| cf0 | foreground color associated with the number 0 in the color table |
Should be:
| \cf0 | foreground color associated with the number 0 in the color table |
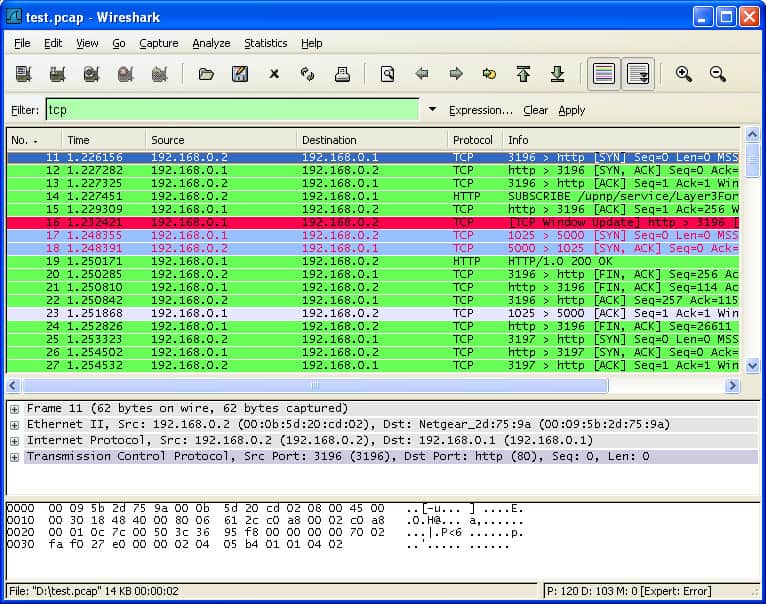
https://www.comparitech.com/net-admin/how-to-use-wireshark/