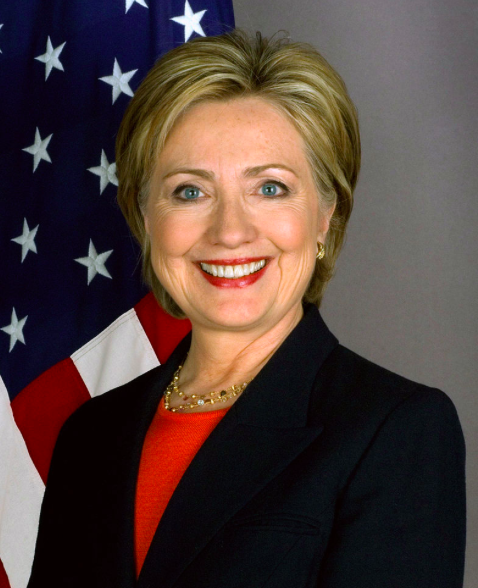
Hillary Clinton as secretary of state
Posted on 10/16/2016 3:54:47 PM PDT by annalex
by sattkisson on September 30, 2016 in Benghazi, News 98 Comments
The FBI could not review all of the Hillary Clinton emails under investigation because:
Justin Cooper: President Bill Clinton aide
Bryan Pagliano: Computer technician from Hillary Clinton ‘08 campaign
Huma Abedin: Hillary Clinton aide
Eric Boswell: State Dept. Assistant Secretary for Diplomatic Security
John Bentel: State Dept. Information Technology official who handled Hillary Clinton’s issues
Jake Sullivan: Hillary Clinton aide
Cheryl Mills: Hillary Clinton chief of staff and attorney
Raymond Maxwell: Former State Dept. Deputy Assistant Secretary
Monica Hanley: Hillary Clinton aide
Sid Blumenthal: Hillary Clinton friend and adviser
Heather Samuelson: Hillary Clinton campaign worker and attorney
David Kendall of Williams & Connolly: Hillary Clinton attorney
3 Known Clinton Private Servers: Apple, “Pagliano,” and Platte River Networks (PRN)
2007: Hillary Clinton announces run for President. Bill Clinton aide Justin Cooper buys an Apple server for a new email system to be located in the Clintons’ Chappaqua, NY residence.
June 2008: Hillary drops out of Presidential race. Cooper sets up the Apple server.
Fall 2008: Hillary aide Huma Abedin contacts Hillary campaign computer tech Bryan Pagliano to build 2nd server because the Apple—in use for just a few months—is “antiquated.”
Jan. 2009: Hillary begins transitioning from her personal BlackBerry.net email to a clintonemail.com account on the “antiquated” Apple server.
Jan. 11, 2009: Increase in cyberattack attempts on State Dept. employee personal email accounts.
Jan. 21, 2009: Hillary becomes secretary of state. She declines a State Dept. email address and instead uses her personal BlackBerry in office.
Feb. 2009: Hillary travels to Asia, her first overseas trip as secretary of state.
March 2, 2009: Security memo warns Hillary and Chief of Staff Cheryl Mills that it’s risky to use their personal email and BlackBerry devices.
I cannot stress too strongly…that any unclassified BlackBerry is highly vulnerable in any setting to remotely and covertly monitoring conversations, retrieving e-mails, and exploiting calendars. –State Dept. memo from Eric Boswell of Diplomatic Security 3/2/2009.March 11, 2009: Hillary is told there’s “intelligence concerning this vulnerability during her recent [Feb.] trip to Asia.” She acknowledges to Boswell that she “gets it.”
March 2009: State Dept. official handling Hillary computer security issues, John Bentel, reportedly receives memo showing that Hillary’s private server was set to be installed at her NY home. Bentel would later tell FBI he didn’t know Hillary was using a personal account or server.
March 18, 2009: The server installed by Pagliano replaces the Apple, but Pagliano later tells FBI he didn’t transfer Hillary’s clintonemail.com account. The FBI could never locate or examine Apple server to determine facts.
Feb. 9, 2011: State Dept. staff again raises concerns about Hillary and staff using electronic devices in their offices.
March 2, 2011: State Dept. detects malicious cyber activity aimed at senior officials.
April 2011: Hillary’s immediate staff is briefed again on cybersecurity threats.
May 2011: Hillary’s immediate staff is briefed again.
Aug. 30, 2011: Hillary requests a government device to replace her broken BlackBerry. After she’s told it would be subject to Freedom of Information Act records searches, no government device is issued.
2011: Memo from Hillary cautions State Dept. employees about security and records retention, and advises not to use personal email for government business.
Sept. 11, 2012: Islamic extremist terrorists attack Americans in Benghazi, Libya.
Nov. 2012: State Dept. Accountability Review Board convenes to investigate Benghazi. Hillary aides Cheryl Mills and Jake Sullivan are reportedly seen at allegedly improper Benghazi “document sorting” session in State Dept. basement.
Week of Dec. 9, 2012: Hillary faints and falls, suffering a concussion. State Dept. keeps it secret for several days.
Dec. 4, 2012:
Dec. 15, 2012: Hillary postpones her Congressional testimony on Benghazi due to illness.
Dec. 30, 2012: State Dept. discloses discovery of “blood clot” in Clinton’s head from the concussion.
Early 2013: Pagliano plans to seek other work. Clinton staff begins searching for vendor to manage a new, 3rd Clinton email server.
Jan. 2, 2013: Platte River Networks of Denver (PRN) wins contract for new Clinton server.
Jan. 7, 2013: Hillary returns to work.
Jan. 23, 2013: Hillary testifies to Congress on Benghazi attacks.
Feb. 1, 2013: Hillary’s last day as secretary of state. She fails to produce her federal records as required by law.
Spring 2013:
March 14, 2013: Hillary confidant Sid Blumenthal’s AOL email is hacked by Romanian cyber hacker “Guccifer,” uncovering a memo to Hillary with classified “confidential” information.
June 2013: According to a book later written by Bill, Hillary finally recovers from her Dec. 2012 illness about now.
June 23, 2013: Pagliano server is moved to Equinix datacenter, NJ which “serves the world’s largest financial, media, and enterprise companies.”
Read: The Definitive Hillary Email Timeline (prior to FBI report)
June 30, 2013: Pagliano server email accounts are transferred to the new PRN server.
July 18, 2013: Clintons sign formal deal with PRN for new email server.
Early 2014: Hanley says she finds Apple MacBook laptop from Spring of 2013 at her home and tries, but fails, to remotely transfer Hillary email archive to PRN server.
Feb. 2014:
May 8, 2014: House Benghazi committee is established.
Summer of 2014: State Dept. notifies Hillary aide Cheryl Mills that it will be requesting Hillary’s work emails.
July 23, 2014: Congressional Benghazi committee reaches agreement with State Dept. on production of records.
July 2014:
August, 2014: State Dept. provides House Benghazi Committee with eight emails to or from Clinton that show her use of a private email account.
Sept. 15, 2014: Sharyl Attkisson reports on State Dept. official who said he witnessed Benghazi document sorting session with Hillary aides in State Dept. basement in 2013.
Late Sept. 2014:
Dec. 2014: Hillary and Abedin begin using new email accounts on the domain hrcoffice.com.
Dec. 5, 2014: Hard copies of Hillary work emails are given to State Dept.
Dec. 2014: Hillary instructs her staff she no longer needs to keep the remaining “personal” emails.
Dec. 2014 or Jan. 2015:
July 10, 2015: FBI begins investigation Hillary email situation after U.S. Intelligence Community Inspector General refers the case of possible improper handling of classified information.
March 2, 2015:
March 3, 2015: House Benghazi committee requests Hillary attorneys at Williams & Connolly to preserve and produce all documents and media related to her two clintonemail.com known addresses.
March 4, 2015: House Benghazi committee privately subpoenas all Hillary emails related to Benghazi terrorist attacks. Clinton does not disclose the subpoenas but tweets, “I want the public to see my email. I asked State to release them. They said they will review them for release as soon as possible.”
March 9, 2015: Mills emails PRN and makes reference to the preservation request from Congress. A PRN technician would later tell FBI he doesn’t remember seeing it.
March 10, 2015: Clinton answers questions about her email practices for the first time. She tells reporters:
March 25, 2015:
March 31, 2015: There’s a conference call among PRN, Kendall and Mills. Later, PRN would exert attorney-client privilege and refuse to comment on conversation. This means Hillary’s attorneys are representing the PRN technician, too.
May 27, 2015: In a Freedom of Information (FOI) lawsuit, the court orders State Dept. to post emails on FOI website on a monthly schedule to complete by Jan 29, 2016. (State completes Feb 29, 2016.)
July 28, 2015: Hillary revises her statement regarding classified email to say she is confident she never sent or received emails that were classified at the time. Later, the FBI would find Hillary sent or received 193 emails (81 separate email conversations) that were classified at the time they were sent, ranging from “Confidential” to “Top Secret/Special Access Program.”
July 31 2015: The federal judge in a Judicial Watch FOI suit, Emmet Sullivan, orders State Dept. to request that Mills and Abedin confirm, under penalty of perjury, that they have produced all government records in their possession, return any other government records immediately, and describe their use of Hillary’s email server to conduct government business.
Aug. 5, 2015: State Dept. sends letter to Hillary including Judge Sullivan’s order.
Aug. 6, 2015: Mills’ attorney tells Judicial Watch that it has instructed Mills to “delete any and all electronic copies [of potential federal records] in her possession” after her anticipated production of records on Aug. 10. Judicial Watch files an emergency request to block the destruction.
Aug. 11, 2015: Inspector General report to the Senate contradicts Hillary claims; some emails, says the IG, contained information that was classified at the time.
Aug. 19, 2015: Hillary’s personal lawyer tells a Senate committee that all data, including emails, was erased from her server prior to it being turned over to the FBI. Hillary tells reporters the investigation surrounding her server “has nothing to do with me.” She contradicts the Inspector General by reiterating that she never sent or received classified material.
Aug. 2015:
Aug. 27, 2015: Hillary tells an Iowa audience that using a personal email server “…clearly wasn’t the best choice..I take responsibility…” She repeats her modified statement, “I never sent nor received any e-mail that was marked classified.”
Sept. 10, 2015: Pagliano pleads the fifth before House Benghazi committee.
October, 2015: Previously withheld Hillary emails reveal she told daughter Chelsea almost immediately that terrorists were behind the Benghazi attacks, yet told the public they were prompted by a protest over a YouTube video.
Oct. 3, 2015: After learning about additional Pagliano server equipment, and that Hillary emails had been transferred to PRN server, FBI obtains equipment and PRN server.
Oct. 14, 2015: Hillary attorneys at Williams & Connolly review an iMac of Hillary’s and assure the Justice Dept. that no work emails were found on it.
Oct. 16, 2015: Williams & Connolly provides 2 Hillary Blackberry devices to FBI but forensics finds no evidence they were ever connected to her personal servers. They do not contain their SIM cards or SD secure digital cards.
Oct. 28, 2015: State Dept. sends formal request to Hillary and other former secretaries asking for their work-related emails. Hillary directs attorneys Kendall and Mills to oversee.
Jan. 7, 2016: FBI interviews Sid Blumenthal, who sent at least 24 memos currently classified “confidential” and at least one email classified as “Secret” at the time and currently to Hillary on unclassified system.
Feb. 9, 2016: Justice Dept. requests all of Hillary’s 13 mobile devices.
Feb. 22, 2016: Williams & Connolly tells DOJ it cannot locate any of the devices, so FBI was unable to examine the 13 mobile devices.
Feb 27, 2016: Jake Sullivan is interviewed by FBI. He says he’s not concerned emails with classified information that he sent to Hillary on unclassified system.
March 2016: Bentel declines to testify to Senate committee.
March 31, 2016: Guccifer is extradited from Romania to US.
April 5, 2016: FBI interviews Huma Abedin who sent at least one email classified as “confidential” to Hillary on her unclassified system.
April 9, 2016: Cheryl Mills is interviewed by FBI. She refuses to answer some questions under attorney-client privilege. She says she’s not concerned by her decision to send Hillary emails with information later deemed “classified” on her unclassified system.
May 25, 2016:
June 22, 2016: Pagliano pleads the fifth 125 times in deposition with conservative watchdog Judicial Watch.
June 27, 2016: Attorney General Loretta Lynch meets privately with President Clinton. The two say it was a purely social visit.
July 2, 2016: FBI interviews Hillary Clinton.
July 4, 2016: Hillary indicates that, as President, she would likely keep Lynch as attorney general.
July 5, 2016: FBI Director James Comey recommends no prosecution in Hillary email case.

Sharyl Atkinson: Investigative Journalist who tries to give you information others don't want you to have. What you do with it is your own business. Do your own research. Seek advice from those you trust. Make up your own mind.
If you want to be on this right wing, monarchy, paleolibertarianism and nationalism ping list, but are not, please let me know. If you are on it and want to be off, also let me know. This ping list is not used for Catholic-Protestant debates; all confessions are welcome.
Bookmark
Please put me on!
Sure thing. Thank you.
Ping to Sharyl’s List Upchuck :D
Bookmark
Wow.
And Nixon is more guilty, more despised than Mao AND Stalin AND Lenin for erasing 18 minutes of tape ....
Sobering.
Politico reported 07/30/15 that Kendall, Hillary Clinton’s private lawyer, has a thumb drive containing classified information from as many as five U.S. intelligence agencies — but the State Department told POLITICO the law firm is taking “appropriate measures” to secure the files.
The agency declined to detail steps made to protect the sensitive information in attorney David Kendall’s possession, but the issue is raising concern among Republicans on Capitol Hill who’ve criticized Clinton’s handling of the email controversy. The thumb drive has copies of emails Clinton kept on a private server while she served as secretary of state, a trove now known to contain classified documents.
The agency told POLITICO that Clinton “does have counsel with clearance.” Kendall, a prominent Williams & Connolly attorney who defended former CIA director David Petraeus against charges of mishandling classified information, declined to comment.
Clinton’s campaign echoed the State Department. “The thumb drive is secure,” said Nick Merrill, a spokesman for the Democratic front-runner’s presidential campaign, referring questions to state.
Senate Judiciary Committee Chairman Chuck Grassley (R-Iowa) has asked the FBI to confirm that the thumb drive has been secured. “This raises very serious questions and concerns if a private citizen is somehow retaining classified information,” Grassley’s said in a letter sent late last week. He asked for more information on Kendall’s clearance and whether the lawyer was authorized to “be the custodian of classified national security information.” The FBI has not yet responded.
SOURCE Read more: http://www.politico.com/story/2015/07/hillary-clinton-email-thumbdrive-security-120833#ixzz4NFevKf19
cont
<><> opening up the e-mail scandal to further questions;
<><> compromising L/E to evade prosecution;
<><> the reckless mishandling of classified information
<><> exposing our national-defense secrets to hostile powers;
<><>the mass destruction of 1000's of government records after Congress requested them;
<><>the obstruction of government investigations;
<><>the serial lies to Congress and to the public;
<><>the shocking failure to provide security for Americans stationed in Benghazi;
<><> making no attempt to rescue Americans during the terrorist siege in Benghazi;
<><>lying to Americans and to murdered Americans' families about the attack's cause;
<><> inventing a video story to cover inaction in Benghazi;
<><> the trumping up of a prosecution against the video producer;
<><> unbecoming conduct by scapegoating a video producer;
<><>the Clinton Foundation corruption visited on the State Dept;
<><> the sale of State Dept influence for foundation donations;
<><> perks, privileges and favors for shady donors at the expense of national security,
<><> the use of the State Department as an arm of the Clinton pay-to-play enterprise;
<><> profiting by stealing State Dept data belonging to the citizenry.
<><> rampant cronysism;
<><> using the State Dept budget as a personal ATM;
<><> turning the State Dept into a racketeering enterprise;
<><> conducting political activites on govt time.
 there's enough right there to put away over a dozen people NOT named Bill or HilLIARy Clinton...
there's enough right there to put away over a dozen people NOT named Bill or HilLIARy Clinton...
The sheer volume shows both sophistication and conscious design: it was a communications system deliberately built to handle sensitive documents bypassing government information security guidelines.
It was nothing like casual and personal communications that a politician or a public servant might wish to set up for her privacy.
So the question becomes: what was the purpose?
The recently leaked Podesta emails and leaked conscripts of clandestine speeches to foreign leaders shone a light on the question of purpose. The system was designed to be a secret communications channel to an elite worldwide community. Deniability and destructibility was built into the system: what we see now, with servers and backup drives disappearing or getting bleached clean of the data, is not incompetence. It was a way to communicate goals, methods and operations clearly, bypassing official channels, and then destroying the evidence.
The purpose was treason.
PLEASE TELL me IT’S being reported by the MEDIAPUKES outlets please!!!
.
BFL
.
I’m shaking with SHEER ANGER!! Dear God PLEASE HELP US..PLEASE!!!!!!!!!!!!!!!!!
This is an excellent research project!
Thanx for posting.
Clift notes version: hildabeast basically say FU to the laws
You will never see this list in the public media.
red
Jesus Christ: You can't impeach Him and He ain't gonna resign.

Fox News Judge Jeanine Pirro preview from the Trump camp on Justice at 9 PM ET.
Of course not. Their method is to
1. Trivialize the purpose. Originally it was, according to them, to have a private life similar to how Colin Powell had it. This is hard to do when you have several servers, smartphones and backup systems destroyed in violation of a subpoena.
2. Trivialize the crime. Systematic destruction of evidence is never brought up; instead it is always some hapless junior help smashing a Blackberry without Hillary’s knowledge.
3. Lying about the security levels. Examples are given of confidential level violated (that is lower level) and of classification expiring on some of them. The complete picture (including 8 top secret items) is never emerging.
4. Presenting a complex and voluminous nature of the security breach as incompetence or forgetfulness, — a series of mishaps by an aging woman lacking information technology savvy. Instead, a massive and brazen, conscious violation of basic information security requirements should be a story in itself, — but it never was.
Disclaimer: Opinions posted on Free Republic are those of the individual posters and do not necessarily represent the opinion of Free Republic or its management. All materials posted herein are protected by copyright law and the exemption for fair use of copyrighted works.