Prayer PrayerRequest SCOTUS ProLife BangList Aliens HomosexualAgenda GlobalWarming Corruption Taxes Congress Fraud MediaBias GovtAbuse Tyranny Obama Biden Elections POLLS Debates TRUMP TalkRadio FreeperBookClub HTMLSandbox FReeperEd FReepathon CopyrightList Copyright/DMCA Notice Donate
Monthly Donors · Dollar-a-Day Donors · 300 Club Donors
FREEPER ALERT! Our FReepathon has fallen way, way behind. Please consider donating today.
or by or by mail to: Free Republic, LLC - PO Box 9771 - Fresno, CA 93794
| Free Republic 2nd Qtr 2024 Fundraising Target: $81,000 | Receipts & Pledges to-date: $20,305 | |||
| ||||
| Woo hoo!! And we're now over 25%!! Thank you all very much!! God bless. | ||||
Posts by Bobalu
-
US official urges China, Russia to declare only humans, not AI, control nuclear weapons
-
Gilroy Man Charged With Murder in Fentanyl Overdose of Baby
If through my stupidity and recklessness I caused the death of a toddler I would just want to be dead, there’s no coming back from such a thing.
I think most Freepers would agree....
-
Live updates: Iranian attack begins, sirens across Israel
Stay close to your shelter my FRiend!
-
Iran launches attack against Israel using dozens of drones
We got the game on here!
-
McDonald's $25 Deal Angers Customers, Shows Damage California's $20 Minimum Wage Is Doing to Fast-Food Industry
When I was in Jr High I usually ate lunch at a White Castle that was near the school.
4 sliders, a fry and a large orange soda...
It was like 1.65 and that seemed like a lot at the time.
Lunch at school was 35 cents but it was sold at a loss I’m sure... extra cartons of milk were a nickle or a dime for chocolate...
A Hershey bar was 5 cents
My dad made about 12 bucks an hour and it was enough to run the household and also put something in savings and supported the cost of an 80 acre farm we used on weekends to get away from the city. (St Louis)
It was about 1968
-
Ballsy: Mexican media outlet gets trolled into airing video of a man’s testicles thinking they were showing the eclipse…
A Baa Baa Booey moment.
Sum Ting Wong
We Tu Low
Ho Lee Phuk -
Roosevelt’s Failure at Yalta.. “I think that if I give him everything that I possibly can and ask nothing from him in return, noblesse oblige, he won’t try to annex anything and will work for a world of democracy and peace.”
FDR was far too leftist and had no great love of constitutionality but the man was at death’s door during the Malta meeting... I can cut him some slack on what happened there... the VP should have already taken over as president long before Yalta.
-
Ham Radio Operators. VANity. Kind of neat.
I have kept my Advanced ticket as it is the ONLY class that proves you did the code ;-)
You can be an extra and not even know how to send a morse SOS call....
I also use morse with microcontrollers... I can hear the text without using something like a crappy 1602 LCD...
-
2024 Total Solar Eclipse: Through the Eyes of NASA (Official Broadcast)....

-
X MARKS THE SHOT
I don’t live very far from the New Madid fault...
I dropped my Lloyd’s of London earthquake insurance from my policy a couple of years ago... perhaps I should go renew that...
If this fault were to go off bigtime though I wonder just how an insurance firm would survive to pay off their obligations... even an outfit as big as Lloyds..
-
Johannesburg's water crisis is the latest blow to South Africa's 'world-class city'
-
The Rise Of Conservative Preppers
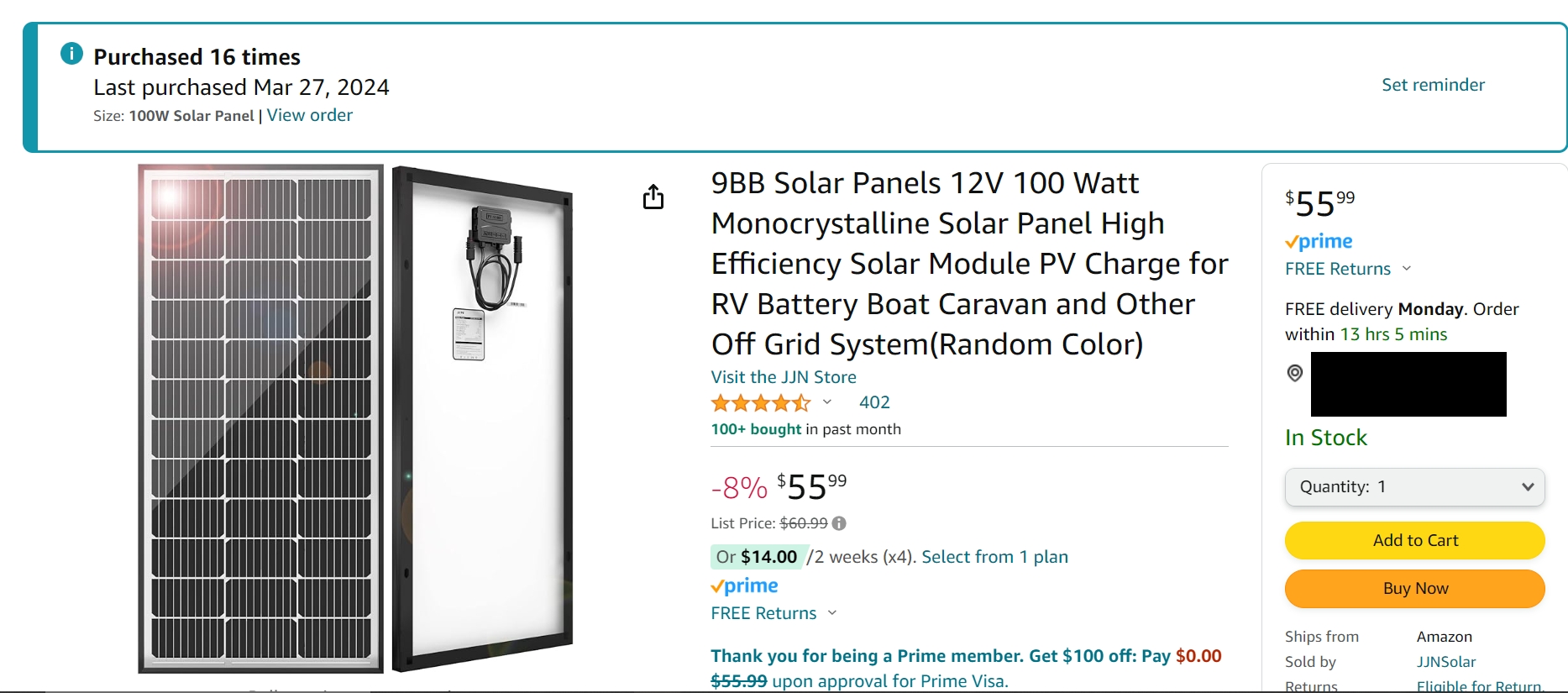
That really is a good price on the pallets of panels!
Thanks!
-
Questions raised over Temu cash 'giveaway' offer
I have been buying some pretty good stuff from Temu. I expected it to all be crap but turns out it was good!Just got in a bunch of XH-M603 charge regulator boards.. they cost less than any I ever found before, even cheaper than building my own boards.. sweet
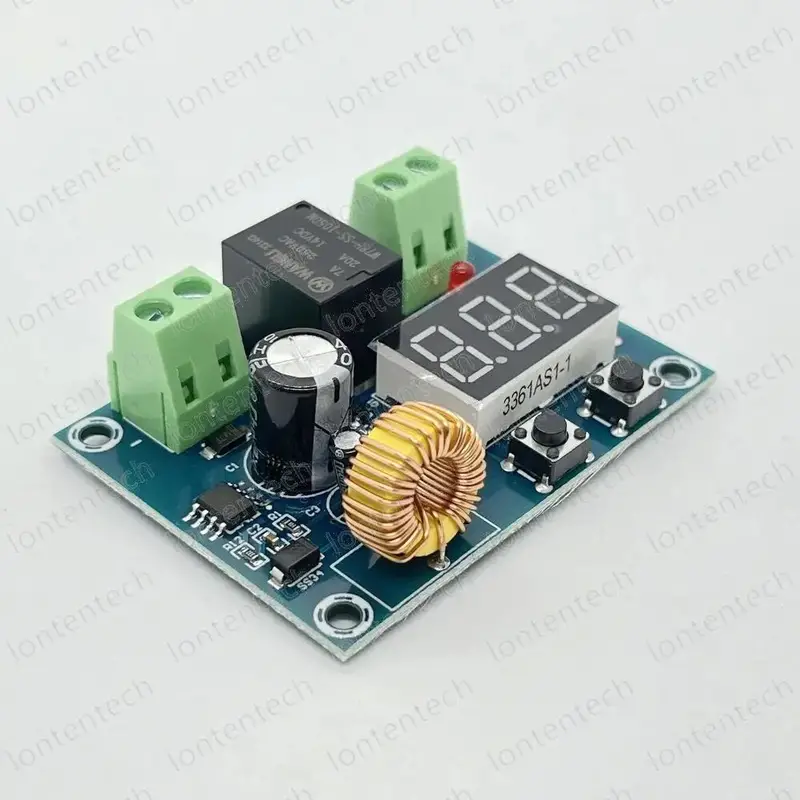
And these nice thermostats w 10A relay, also sweet at two for 3.98 and free shipping.

-
Gavin Newsom caught with hand in cookie jar again, exempts more 'friends' from $20/hour fast-food wage law
Down N Out Burger
-
The Rise Of Conservative Preppers
It’s solar, the sun powers it
-
The Rise Of Conservative Preppers
What you say is true for a small system but not for a large system.It's best to have a large solar panel array AND and large LiFePO4 battery bank...AND run efficient items like the solar refrigerators/freezers I got, they are energy stingy.
Build your system so that you can get by even if EVERY day from now on will be overcast... you only get 10-20% of your panel rating in such conditions and only for perhaps 6hrs a day at most so OVERBUILD. 20kw of panels will give you 2-4kw for 4-6hrs a day 20kw of panels are selling for roughly 12,000 dollars currently (Amazon) 100kw of panels for roughly 60,000.. Of course you need to live on a farm or something to put out so many panels.. I have 40 acres.
If you don't build for the worst possible case of every day being overcast you will be disappointed with your results.
And if you get clear bright days an overbuilt system can really get you some power... say 20kw+ on a bright day, you can run a clothes dryer during such times... but I'd still rather store the extra and hang the clothes out :-)
Be aware that the copper wiring for a large system is pretty costly.. 2 aught copper ain't cheap and it's best to run a 48VDC system so you can use smaller/cheaper wiring :-/
Also get enough AC charge capability so if your power from the grid is intermittent you can top up your battery bank... but don't depend on that, again.. OVERBUILD!
These are the panels I am now buying to put in storage.. unconnected in case of EMP, they should survive if not connected to wiring... I have diodes to replace those if the ones on the panel were to blow.
I have about 100 of these and more coming... here they are, it's a good buy for 100watt 9bb monocrystalline panels with free shipping.
-
The Rise Of Conservative Preppers
If the power goes out permanently I want be able to run the following and have put the gear together to make it so.
-microwave ovens
-room air conditioners
-Fans, lots of fans
-refrigerators and small freezers
-Washing machine
-my computers
-My ham radio gear
-simplex repeaters for local comms
-electric blankets
-LED room lighting
-DC chainsaws
-Small power toolsI still need to get the gear together to pump water from my
wells, I can draw water by hand but a pump and pressure tank is a better solution by far.I am not building a solar power system capable of running the electric central heaters or the clothes dryer.. I can hang clothes out to dry them and I live in a vast forest so I have two woodstoves at the ready.
I have gathered together redundant air conditioners, power tools, small refrigerators..etc etc
I have gathered some ammo but I’m not much of a gun guy.
I have a 22 rifle and a 12 gauge pump shotgun and hundreds of rounds for them.Lots of security gear, doppler motion sensors, 8 cam security system..etc
LOTS of foodstuffs, medicines, surgical instrument sets..etc
I still need to stock some IV fluids and more bandages and such... I also need to get some O2 concentrators..I have about 20 good GPS drones for surveillance use.
I still think of at least one more thing each day that I need to get... I know I will forget several things but what can you do...
I have EMP storage for Ham and solar gear, this is just several large galvanized trash cans. 40 spare solar panels that are not connected, still factory packaged.. these should survive any EMP.
My car is old and likely will survive EMP, I got ten 5gal cans for gas... I was shocked at how much a simple 5gal gas can costs! :-/
I have the gear to assemble a mesh network that would cover the county I live in.
I have some FM band transmitters and could cover the local area with a signal if it came to that.
I have four 65’ fiberglass telescoping antenna poles for repeaters and the mesh network.... and nice tall hills on the property for them.
I’m a frugal guy (cheap) but I felt the need to prepare.
I hope to God I never have to use any of it!Be prepared my FRiends!
-
OP-ED: The Baltimore Bridge Disaster By Supply Chain Expert and Navy Veteran Jim Nelles

-
WHAT IS THE GOSPEL
-
OP-ED: The Baltimore Bridge Disaster By Supply Chain Expert and Navy Veteran Jim Nelles

Get Connected! Join Free Republic Today!
Already a Member? Log into your Free Republic account.
- FREEPER ALERT! Our FReepathon has fallen way, way behind. Please consider donating today.
- White House: We Have Job Market That’s ‘Better Than Even a Soft Landing’
- NYU protestors call for 'death to America' and 'long live the intifada' in horrifying notes in their 'Gaza' camp
- As a Jew, I Am Terrified About What America Has Become
- ‘The Guy Is a Monster’: Robert de Niro Says Trump’s Rise Is Like Hitler’s
- Trump suggests when he might make VP pick as these four contenders reportedly emerge
- Biden to Award Medal of Freedom to Kerry, Gore, and others
- Live thread [05/03/2024]: Trump show trial in New York, brought to you by Biden operative Matt Colangelo; post comments here
- Biden Administration Has Cemented $1 Trillion Worth Of Rules And Regulations In 2024, Analysis Finds
- Joe Biden to Anti-Israel Protesters: You Have Failed, Have Not Forced Me to Reconsider Policies
- More ...
- ‘The Chosen’ TV Show is Coming to Disney+ and Hulu in Major ‘Partnership’
- Biden's Economic Adviser Tries and Fails To Explain How Money Works
- Fani Willis Hired Nathan Wade Without Fulton County’s Input, Officials Say
- Bruni: Young Progressives Never Acknowledge Horrific October 7 Attack, They Advocated for Hamas
- Banning Trump from talking about his trial is blatant election interference
- Fani Willis grilled during hearing over amount of money spent on prosecuting Trump case -- instead of county's backlog of criminal cases
- FULL INTERVIEW: Arizona Rancher George Kelly Reveals What Really Happened on Night He Was Arrested and Taken to Jail Full of Cartel Members (VIDEO)
- DOJ warns Iowa that it would be sued if it enforces new immigration law
- Jeff Daniels: Midwesterners Are Done with Trump’s ‘Lack of Decency’
- U.S. Government Helps Pro-Ukraine Media Spread Propaganda And Silence American Critics
- More ...