Posted on 01/22/2011 7:01:38 PM PST by lbryce
Amid all of the media and public fascination with threats like Stuxnet and weighty terms such as “cyberwar,” it’s easy to overlook the more humdrum and persistent security threats, such as Web site vulnerabilities. But none of these distractions should excuse U.S. military leaders from making sure their Web sites aren’t trivially hackable by script kiddies.
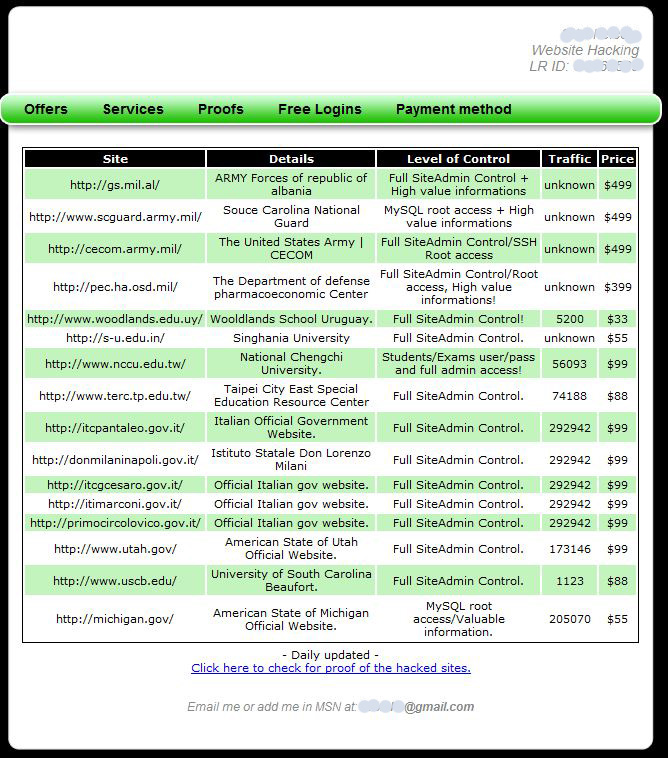
Security vendor Imperva today blogged about a hacker who claims to have access to and control over several top dot-gov, dot-mil and dot-edu Web sites. I’ve seen some of the back-end evidence of his hacks, so it doesn’t seem like he’s making this up. Perhaps out of deference to the federal government, the Imperva folks blocked out the best part of that screen shot — the actual names of the Web site domains that this hacker is selling. For example, the hacker is advertising full control and root access to cecom.army.mil, a site whose stated purpose is “to develop, acquire, provide and sustain world-class…systems and Battle Command capabilities for the joint warfighter.” It can be yours, for just $499 (sorry, no credit cards accepted; only the virtual currency Liberty Reserve).
Here is an unredacted (well, mostly) shot of that site:
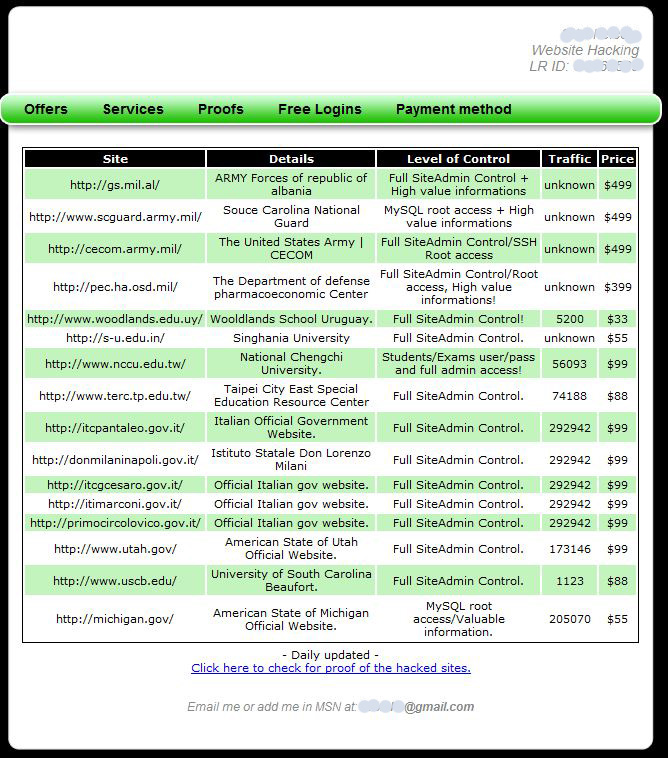
According to Imperva, this enterprising hacker is also selling info personally identifiable information from hacked sites, for $20 per 1K records. The company mined this hacker’s postings on other forums, and found evidence that he was able to hijack the sites via SQL injection vulnerabilities, most likely with the help of an automated vulnerability scanner.
<

(Excerpt) Read more at krebsonsecurity.com ...
 and this is legal???
and this is legal???
No. The word “illegal” in the title indicates it is NOT legal.:-)
 it says the access you buy is illegal... i'm talking about advertising it!!!
it says the access you buy is illegal... i'm talking about advertising it!!!
Disclaimer: Opinions posted on Free Republic are those of the individual posters and do not necessarily represent the opinion of Free Republic or its management. All materials posted herein are protected by copyright law and the exemption for fair use of copyrighted works.