
Posted on 08/28/2009 10:58:25 AM PDT by ShadowAce
Computer scientists in Japan say they've developed a way to break the WPA encryption system used in wireless routers in about one minute.
The attack gives hackers a way to read encrypted traffic sent between computers and certain types of routers that use the WPA (Wi-Fi Protected Access) encryption system. The attack was developed by Toshihiro Ohigashi of Hiroshima University and Masakatu Morii of Kobe University, who plan to discuss further details at a technical conference set for Sept. 25 in Hiroshima.
Last November, security researchers first showed how WPA could be broken, but the Japanese researchers have taken the attack to a new level, according to Dragos Ruiu, organizer of the PacSec security conference where the first WPA hack was demonstrated. "They took this stuff which was fairly theoretical and they've made it much more practical," he said.
They Japanese researchers discuss their attack in a paper presented at the Joint Workshop on Information Security, held in Kaohsiung, Taiwan earlier this month.
The earlier attack, developed by researchers Martin Beck and Erik Tews, worked on a smaller range of WPA devices and took between 12 and 15 minutes to work. Both attacks work only on WPA systems that use the Temporal Key Integrity Protocol (TKIP) algorithm. They do not work on newer WPA 2 devices or on WPA systems that use the stronger Advanced Encryption Standard (AES) algorithm.
The encryption systems used by wireless routers have a long history of security problems. The Wired Equivalent Privacy (WEP) system, introduced in 1997, was cracked just a few years later and is now considered to be completely insecure by security experts.
WPA with TKIP "was developed as kind of an interim encryption method as Wi-Fi security was evolving several years ago," said Kelly Davis-Felner, marketing director with the Wi-Fi Alliance, the industry group that certifies Wi-Fi devices. People should now use WPA 2, she said.
Wi-Fi-certified products have had to support WPA 2 since March 2006. "There's certainly a decent amount of WPA with TKIP out in the installed base today, but a better alternative has been out for a long time," Davis-Felner said.
Enterprise Wi-Fi networks typically include security software that would detect the type of man-in-the-middle attack described by the Japanese researchers, said Robert Graham, CEO of Errata Security. But the development of the first really practical attack against WPA should give people a reason to dump WPA with TKIP, he said. "It's not as bad as WEP, but it's also certainly bad."
Users can change from TKIP to AES encryption using the administrative interface on many WPA routers.

Pingaling
So much for security on my Wi-Fi at home. Guess it’s back to hardwiring for now.

My home office wireless router was installed by Verizon, and it has a WEP key printed right on the side of the unit. Should I be worried? Freeper experts, any feedback on how an average user can protect their wireless networks?
If somebody wants to hack something bad enough and they have the time to do it, they will always find a way.
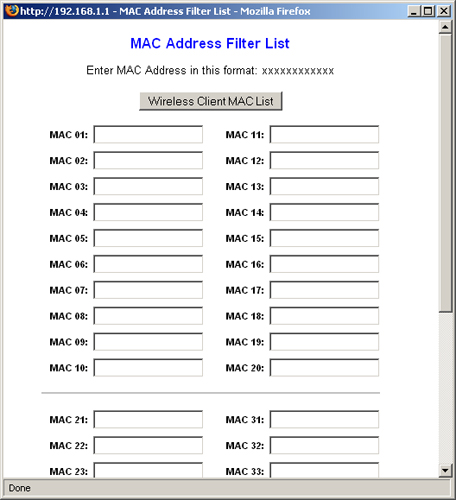
MAC filtering will prevent connection to and use of the WAP. But will it prevent the interception and decryption of wireless traffic?
Good. WPA2 is safe......for now.
WEP is the weakest of any security. Should be at least WPA.....preferably WPA2 if your router supports it.
I’m in I.T., but not an expert in wireless security. I use MAC filtering, WEP, and non-broadcasted SSID. Not perfect, but it’s the best that my WAP provides.
Don’t forget to change the default login and password for the WAP admin account.
Pinging you Ski, just in case you’re not on the tech list. This is scary.
Pinging you Ski, just in case you’re not on the tech list. This is scary.
You may want to cover it up with a piece of tape.
The main reason to have your wireless network password protected is to keep your neighbors from using your network. Not so much to keep them from getting into your data, but to keep them from stealing your bandwidth (a neighbor kid downloading music and video can impact your speed.)
There are people that drive around looking for home networks to hack into to steal data, but there are so many unsecured (no password) home networks out there that they don’t need to hack into one with a password.
Unless one of your neighbors (or their kids) saw the password and wrote it down you are probably OK.
WPA 2 is pretty well established by now, having been part of the standard with which compliance is required since 2006 in order for the WiFi logo to be used on a product. If you have a pre-2006 router, maybe it’s time to upgrade. First, check to see if a firmware update is available which might provide WPA 2. Else, get a new router. They’re cheap and there have been speed, security and functionality improvements. My personal recommendation, after a lot of research, has been the D-Link DIR-655, for its speed and superb firewall.
yes
MACs can be spoofed quite easily
Go to Staples and buy a new WPA2 wireless router for 30 bucks.
Disclaimer: Opinions posted on Free Republic are those of the individual posters and do not necessarily represent the opinion of Free Republic or its management. All materials posted herein are protected by copyright law and the exemption for fair use of copyrighted works.