Skip to comments.
Republicans for Snowden
WSJ ^
| 7/24/2013
| WSJ Editors
Posted on 07/26/2013 6:48:14 AM PDT by Qbert
Few things are more dangerous than Congress in heat, and so it is this week as a libertarian-left wing coalition in the House of Representatives is rushing to neuter one of the National Security Agency's antiterror surveillance programs.
The chief instigator is Michigan Republican Justin Amash, the 33-year-old second-termer who has made opposition to the country's post-9/11 security programs a personal crusade.
[Snip]
Now he's back with an amendment to this year's defense spending bill that would bar the NSA from collecting metadata except when specific individuals are already being investigated and are subject to a court order. This would effectively end one of the two programs exposed by admitted NSA leaker and fugitive, Edward Snowden.
Metadata are the general phone records—numbers called, duration of the calls—not the content of the conversations. Searching through metadata amounts to searching the haystack to find a needle. But under Mr. Amash's amendment, the NSA could only gather metadata if it has already found the needle.
[Snip]
Several former Bush security officials on Tuesday also released an open letter to Congress supporting the NSA programs as lawful, carefully limited and essential to U.S. security. The signers include former Attorneys General Michael Mukasey and Alberto Gonzales, former CIA directors Michael Hayden and Porter Goss, former national security adviser Stephen Hadley, and former secretary of Homeland Security Michael Chertoff.
By all means Congress should debate the NSA programs now that they are public, but any new limits ought to be carefully vetted for their potential consequences. The last thing Congress should do is kill a program in a rush to honor the reckless claims of Mr. Snowden and his apologists.
(Excerpt) Read more at online.wsj.com ...
TOPICS: Government; News/Current Events; Politics/Elections
KEYWORDS: 113th; amash; snowden; spying
Those of you who are opposed to the government spying on everybody (and then lying about it before Congress) should be ashamed of yourselves...
1
posted on
07/26/2013 6:48:14 AM PDT
by
Qbert
To: Qbert
If they were concerned about security they would secure the border and stop importing muslims.
2
posted on
07/26/2013 6:49:43 AM PDT
by
cripplecreek
(REMEMBER THE RIVER RAISIN!)
To: Qbert
The WSJ would have backed the Brits in 1776. They don’t care about freedom as long as they have the security to keep their money.
3
posted on
07/26/2013 6:51:51 AM PDT
by
txrefugee
To: Qbert
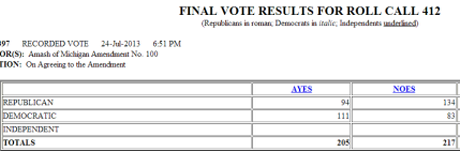
Michigan Republican Justin Amash is a Tea Partier who sponsored the bill to defund bulk collection of American citizens telephone records by the NSA, which is a clear violation of the 4th Amendment. As a fellow Tea Partier, I applaud Amash for his efforts to defend our Constitutional rights, but alas, the big government statists on both sides of the aisle, both Democrats and Republicans, teamed up to continue this unconstitutional spying program. Remember who they are and if you live in their district, do everything you can to defeat them in the upcoming 2014 elections.
4
posted on
07/26/2013 6:55:29 AM PDT
by
rochester_veteran
(All that is necessary for the triumph of evil is for good men to do nothing.)
To: Qbert
Those of you who are opposed to the government spying on everybody (and then lying about it before Congress) should be ashamed of yourselves...
I am. I will accept all of the government intrusion necessary to protect my rights and freedom.
The attitude sort of reminds me of those scrolling shootout video games (e.g. Zaxxon), where destroying the enemy's fuel tanks somehow gives you extra fuel.
5
posted on
07/26/2013 6:57:06 AM PDT
by
Dr. Sivana
(There's no salvation in politics.)
To: Qbert
The last thing Congress should do is kill a program in a rush to honor the reckless claims of Mr. Snowden
Reckless claims?! Of every put forward, NO ONE has suggested that Snowden doesn't have bona fide documents. C'mon WSJ, conservatives are supposed to be above such obvious spin. Emphasizing, de-emphasizing, steering conversation ... those are acceptable rhetorical devices. Talking like the love child of Jay Carney and Nancy Pelosi is not.
6
posted on
07/26/2013 6:59:55 AM PDT
by
Dr. Sivana
(There's no salvation in politics.)
To: cripplecreek
All of this wonderful metadata collection... and they still couldn’t stop two Muslim terrorists from killing and maiming innocent people at the Boston Marathon.
7
posted on
07/26/2013 6:59:58 AM PDT
by
Qbert
("The best defense against usurpatory government is an assertive citizenry" - William F. Buckley, Jr.)
To: rochester_veteran
It was, however, a surprisingly close vote… even if there is a vote-rigging puppeteer, this indicates just how unpopular the program is.
I do wonder however, how the vote would have turned out if the congressmen voted their own consciences
.
8
posted on
07/26/2013 6:59:58 AM PDT
by
OneWingedShark
(Q: Why am I here? A: To do Justly, to love mercy, and to walk humbly with my God.)
To: Qbert
Terrorists could rent every billboard along the length of I-80 and advertize an impending attack 6 months ahead of time and the Neo Stasi Agency would still miss it.
9
posted on
07/26/2013 7:02:29 AM PDT
by
cripplecreek
(REMEMBER THE RIVER RAISIN!)
To: Qbert
Justin Amash, the 33-year-old second-termer who has made opposition to the country's post-9/11 security programs a personal crusade. The terrorists won on 9/11.
This is a radical statement, but look at the way OUR government has used that event to go after each and every one of our Liberties since then! It started under Bush, but 0bama has used it to make himself emperor. Look at how our quasi-dictator, who rules and lives like an emperor, daily flaunts The Constitution. Two events from just yesterday:
1. Holder has declared the Supreme Court ruling on enforcement of the Voting Rights Act not to be of his liking, so he stated that he intends to continue strict oversight and enforcement;
2. 0bama out giving an indoctrination speech, had young Republicans (citizens) banned - this is only one step in banning ALL dissention!
Take a look at Executive Order EO13603. "At a time of the President's choosing, he may seize all food stuffs and water ..." It goes on from there including forced induction into the military. This is just the beginning of broad dictatorial powers.
Flame away!
10
posted on
07/26/2013 7:04:46 AM PDT
by
The Sons of Liberty
(A Quiet Rage is Building All Across America!)
To: Qbert
Oh please - did the NSA stop a plot by two foreginers, warned to us by Russia, who traveled to Chechnya, had criminal records, from pulling off the plot in boston?
These things are not keeping you safer. They are enslaving us.
11
posted on
07/26/2013 7:06:42 AM PDT
by
GlockThe Vote
(The Obama Adminstration: 2nd wave ofo attacks on America after 9/11)
To: Dr. Sivana
"I will accept all of the government intrusion necessary to protect my rights and freedom."
How do you know what is "necessary" if you simply take them at their word (keeping in mind that they have already purposefully deceived you), without asking basic questions?
12
posted on
07/26/2013 7:07:10 AM PDT
by
Qbert
("The best defense against usurpatory government is an assertive citizenry" - William F. Buckley, Jr.)
To: The Sons of Liberty
Seems that a few of our founders warned that tyranny would come to America under the guise of fighting a foreign enemy.
13
posted on
07/26/2013 7:09:55 AM PDT
by
cripplecreek
(REMEMBER THE RIVER RAISIN!)
To: OneWingedShark
It was, however, a surprisingly close vote… even if there is a vote-rigging puppeteer, this indicates just how unpopular the program is.
I do wonder however, how the vote would have turned out if the congressmen "voted their own consciences". Yes, it was close. Here's the graphic for the breakdown of the vote:
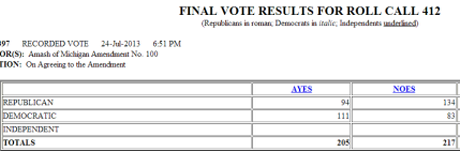
Liberty vs security is a continuing issue and there's a lot of Republicans (and Democrats too, but we already knew that) who ignore the following advice:
Those who would give up essential liberty to purchase a little temporary safety deserve neither liberty nor safety.
--Benjamin Franklin
14
posted on
07/26/2013 7:10:54 AM PDT
by
rochester_veteran
(All that is necessary for the triumph of evil is for good men to do nothing.)
To: cripplecreek
Yep. Meanwhile, College Republicans who simply wanted to listen to a public speech by the president are viewed as potential “terrorists” and turned away...
15
posted on
07/26/2013 7:14:01 AM PDT
by
Qbert
("The best defense against usurpatory government is an assertive citizenry" - William F. Buckley, Jr.)
To: Qbert
Now there is the news that the government is demanding that passwords be handed over.
That could come in real handy for eliminating political enemies. With that kind of access, they could pass child porn around via tea partiers email addresses then send in the FBI to take down the child porn ring.
16
posted on
07/26/2013 7:17:50 AM PDT
by
cripplecreek
(REMEMBER THE RIVER RAISIN!)
To: Dr. Sivana
"Reckless claims?! Of every put forward, NO ONE has suggested that Snowden doesn't have bona fide documents. C'mon WSJ, conservatives are supposed to be above such obvious spin."
Yep. (Btw, I misread your other comment- my bad)
17
posted on
07/26/2013 7:18:45 AM PDT
by
Qbert
("The best defense against usurpatory government is an assertive citizenry" - William F. Buckley, Jr.)
To: txrefugee
“The WSJ would have backed the Brits in 1776. They don’t care about freedom as long as they have the security to keep their money.”
+1. A quote from the movie “Sgt. York” comes to mind: “The cost of that heritage is high. Sometimes it takes all we have to preserve it.” Those who promise security in exchange for our liberty do not value either.
18
posted on
07/26/2013 7:22:50 AM PDT
by
GenXteacher
(You have chosen dishonor to avoid war; you shall have war also.)
To: GlockThe Vote
did the NSA stop a plot by two foreginers, warned to us by Russia,
This is actually the first of the ‘phony scandals’, and Carney should be forced to address it every day, as well.
19
posted on
07/26/2013 7:31:00 AM PDT
by
txhurl
('The DOG ate my homework. That homework, too. ALL my homework. OK?' - POSHITUS)
To: Qbert
Just to review: The 16 major US Intelligence agencies in 7 independent government branches.
1) Central Intelligence Agency (CIA)
2) United States Department of Defense
Defense Intelligence Agency (DIA)
National Security Agency (NSA)
National Geospatial-Intelligence Agency (NGA)
National Reconnaissance Office (NRO)
Air Force Intelligence, Surveillance and Reconnaissance Agency (AFISRA)
Army Intelligence and Security Command (INSCOM)
Marine Corps Intelligence Activity (MCIA)
Office of Naval Intelligence (ONI)
3) United States Department of Energy
Office of Intelligence and Counterintelligence (OICI)
4) United States Department of Homeland Security
Office of Intelligence and Analysis (I&A)
Coast Guard Intelligence (CGI)
5) United States Department of Justice
Federal Bureau of Investigation (FBI)
Drug Enforcement Administration, Office of National Security Intelligence (DEA/ONSI)
6) United States Department of State
Bureau of Intelligence and Research (INR)
7) United States Department of the Treasury
Office of Terrorism and Financial Intelligence (TFI)
**********
The major espionage programs being used against the American public today.
NarusInsight (FBI)
CALEA, the Communications Assistance for Law Enforcement Act (1994) (FBI)
ADVISE (Analysis, Dissemination, Visualization, Insight, and Semantic Enhancement), a massive data mining system run by the DHS.
PRISM - Finally the NSA gets involved. (PRISM is a government codename for a data collection effort known officially as US-984XN.)
“Other systems”, run by the 100+ federal police agencies. There are lots of these.
Much of the raw data from these are compiled with local, state, commercial and medical information into 72 “Fusion Centers” around the US, accessible to many government personnel.
The non-police and non-intelligence related federal agencies keep their own databases and dossiers of personal information of US citizens, as well as engage in intelligence gathering and police activities.
Ironically, the massive installation in Utah that collects and stores vast amounts of civilian data mostly does just that: collecting and storage. It is just in case somebody in government ever wants 10 years of communications to and from somebody they don’t like, even if they aren’t a criminal or suspected terrorist.
20
posted on
07/26/2013 9:29:07 AM PDT
by
yefragetuwrabrumuy
(Be Brave! Fear is just the opposite of Nar!)
Disclaimer:
Opinions posted on Free Republic are those of the individual
posters and do not necessarily represent the opinion of Free Republic or its
management. All materials posted herein are protected by copyright law and the
exemption for fair use of copyrighted works.
FreeRepublic.com is powered by software copyright 2000-2008 John Robinson