Next, there are plenty of careless users of Windows OS devices, who desire convenience instead of conservative management of their device and network softwware (such as Internet browsers, e-mail, text messaging, firewalls, javascript and other script DENY/ALLOW) settings.
Such users "simply" will not use complex passwords. Or, they will use the same password at various websites and for various accounts. Or, they will click on links in e-mail messages (that is very helpful for hackers on phishing expeditions).
In addition, millions of users are glued to Google, regardless of plenty of online information that explains: Using Google is HIGH RISK - exposing behavior and words that reveal user patterns.
Hackers come from the botnets and DNS mist that works for communism and criminals, afforded by the Obama Administration:
- - -
[ALL-AMERICAN] List of DNS Root Servers in 1990 - ICANN WIKI (their table:)
Original Name New Name Organisation SRI-NIC.ARPA NS.NIC.DDN.MIL SRI International A.ISI.EDU A.ISI.EDU Information Science Institute, USC C.NYSER.NET C.NYSER.NET Rensselaer Polytechnic Institute TERP.UMD.NET TERP.UMD.NET University of Maryland GUNTER-ADAM.ARPA GUNTER-ADAM.AF.MIL U.S. Air Force Networking Group NS.NASA.GOV NS.NASA.GOV NASA Ames BRL-AOS.ARPA AOS.BRL.MIL Ballistic Research Laboratory, U.S. Army
On 28 July 1991, the server NIC.NORDU.NET was added to the root zone and became the first non-U.S. root server, located in Sweden. A.ISI.EDU was retired. RSSAC023: History of the Root Server System - Friday 11/04/2016
Name IP Address Organisation NS.NIC.DDN.MIL 192.112.36.4 Network Solutions, Inc. KAVA.NISC.SRI.COM 192.33.33.24 SRI International C.NYSER.NET 192.33.4.12 NYSERnet TERP.UMD 128.8.10.90 University of Maryland NS.NASA.GOV 128.102.16.10, 192.52.195.10 NASA Ames Research Center NIC.NORDU.NET 192.36.148.17 NORDUnet [Sweden] AOS.BRL.ARPA 192.5.25.82 Ballistic Research Laboratory, U.S. Army
- - -
Attack floods Internet root servers with 5 million queries a second - Wednesday 12/09/2015
[EXCERPTS]Perhaps more concerning, the junk queries were received by name servers that use IP Anycast, a network routing method that assigns the same public IP address to multiple geographically dispersed servers. Since the attack was observed hitting Anycast machines, that means the significant resources that made them possible were also geographically dispersed rather than being from a handful of sources in just a few locations.
"This event was notable for the fact that source addresses were widely and evenly distributed, while the query name was not," an advisory published Friday noted. "This incident, therefore, is different from typical DNS amplification attacks whereby DNS name servers (including the DNS root name servers) have been used as reflection points to overwhelm some third party."
A large botnet of infected computers or other Internet-connected devices is the most plausible explanation for such an attack.
Since 2003, Intel-based machines have been used exclusively. - Tuesday 09/21/2021
The number of DNS Root Servers grew to 13.
- - -
7 Days Before Obama Gives Away Internet & National Security - Saturday 09/24/2016
Before 10/01/2016, ICANN performed management responsibility under oversight of the National Telecommunications and Information Administration (NTIA), an agency of the United States Department of Commerce. - Wikipedia
- - -
DNS Root Servers: What Are They and Are There Really Only 13? - Friday 07/30/2021
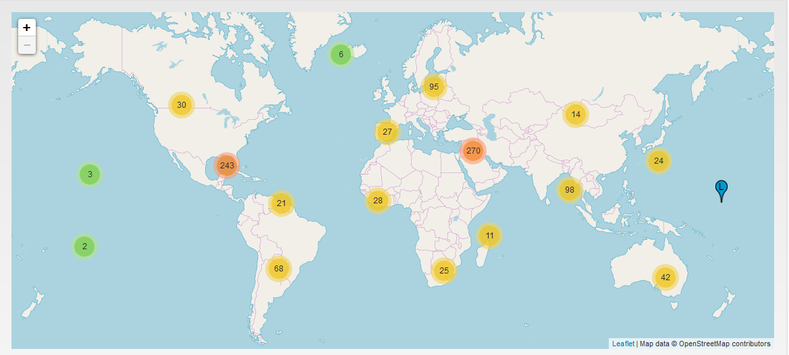
Location of the DNS Root Servers. The 13 root name servers, designated by letters A thru M, are operated by 12 independent organisations. Details about each DNS Root Server Operator, can be found at that Root-Servers.org website. Map of the DNS Root Server System:
A Deep Dive on the Recent Widespread DNS Hijacking Attacks - Monday 02/18/2019